What is HSTS and why is it in my ASP.NET Core app?
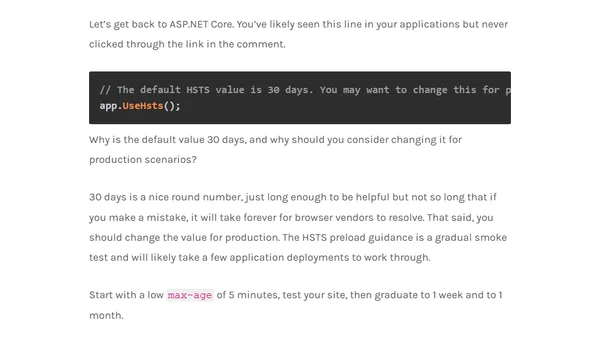
Explains HSTS (HTTP Strict Transport Security), its role in ASP.NET Core apps for enforcing HTTPS, and configuration considerations.
Explains HSTS (HTTP Strict Transport Security), its role in ASP.NET Core apps for enforcing HTTPS, and configuration considerations.
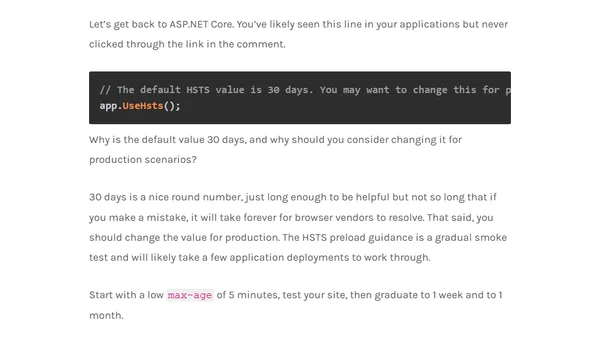
Explores using a local SSH server as a secure alternative to sudo for privilege management, avoiding setuid binaries.
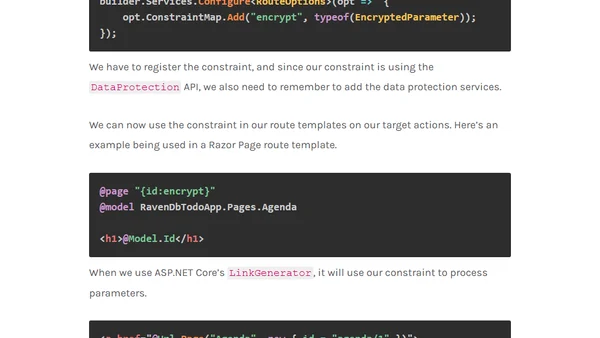
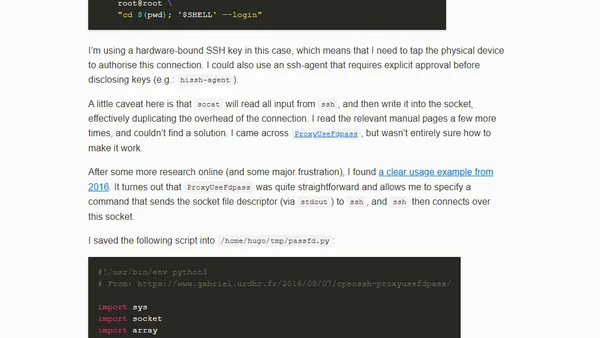
A guide to encrypting and decrypting sensitive identifiers in ASP.NET Core route parameters for improved security and data privacy.

A former Microsoft Azure Data security Program Manager reflects on their role, the impact of improving SQL's permission system, and reasons for leaving.
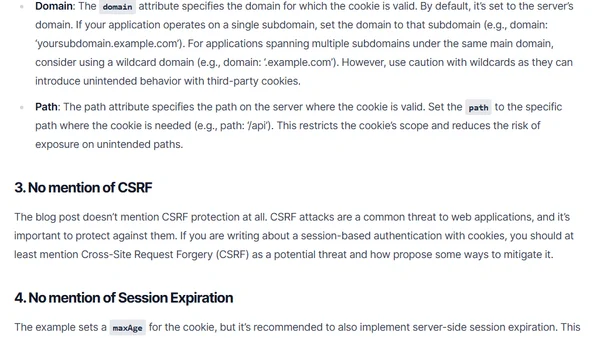
Analyzes common security flaws in Express.js authentication, focusing on hardcoded secrets and poor cookie configuration, with solutions.
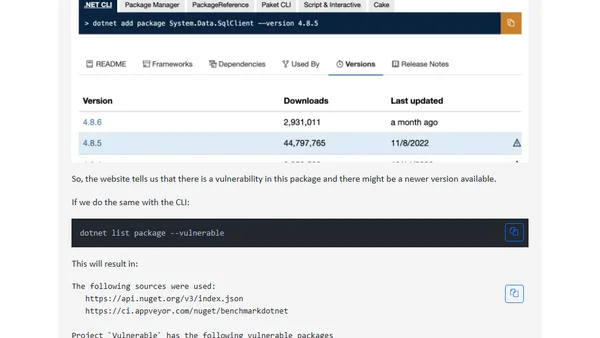
Learn how to use the dotnet CLI to check your .NET solution for NuGet packages with known vulnerabilities or that are deprecated.
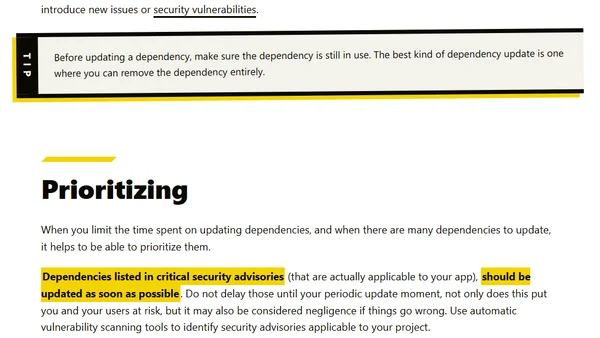
Discusses the challenges of keeping software dependencies updated and compares manual vs. automated strategies for managing updates effectively.
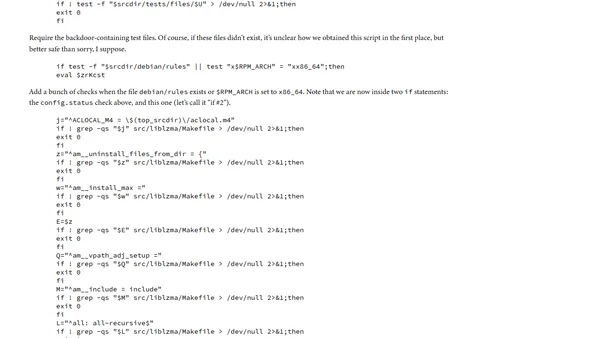
Analysis of the malicious shell script component in the xz backdoor attack, detailing its injection and execution mechanisms.
Discusses the retirement of Azure's default outbound access for VMs in 2025, explaining the security reasons and urging preparation.
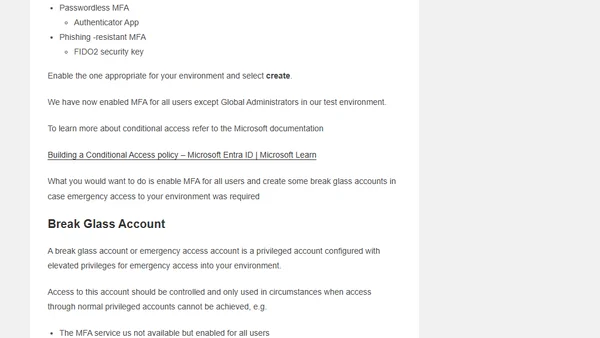
A technical guide on securing user identity in Azure Entra ID, covering MFA, Conditional Access, break glass accounts, and other security configurations.
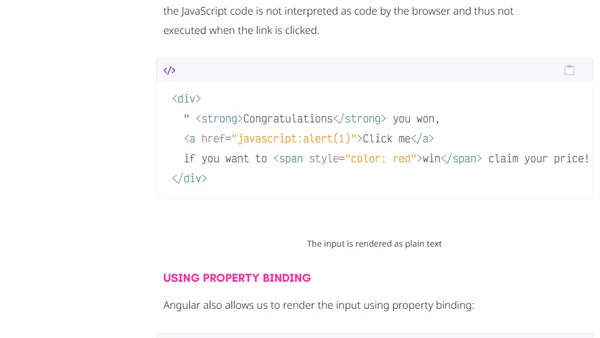
Explains how Angular's built-in security features automatically protect web applications from Cross-Site Scripting (XSS) attacks by sanitizing untrusted values.

An open source maintainer explains why automated security reports about nested dependencies are often unhelpful and asks developers to stop sending them.
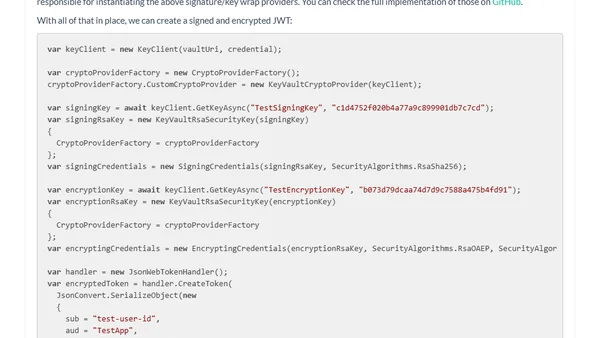
Explains how to use Azure Key Vault keys for signing and encrypting JSON Web Tokens (JWTs), including key rotation.
Explains the limitations of code signing for software security and introduces software provenance as a more robust alternative.

A developer's prank NPM package called 'everything' that depends on all public packages causes dependency chaos and highlights registry policy flaws.
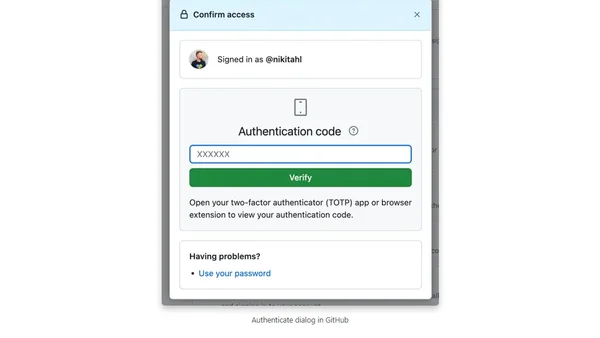
A step-by-step guide on how to change the TOTP-based two-factor authentication app linked to your GitHub account.
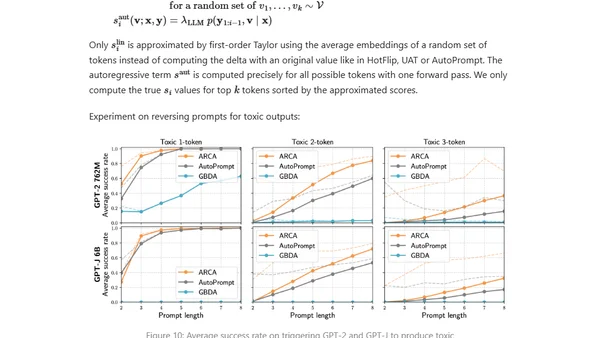
Explores adversarial attacks and jailbreak prompts that can make large language models produce unsafe or undesired outputs, bypassing safety measures.
A fable about a security guardian and a developer learning to collaborate, illustrating the principles of DevSecOps and secure software development.
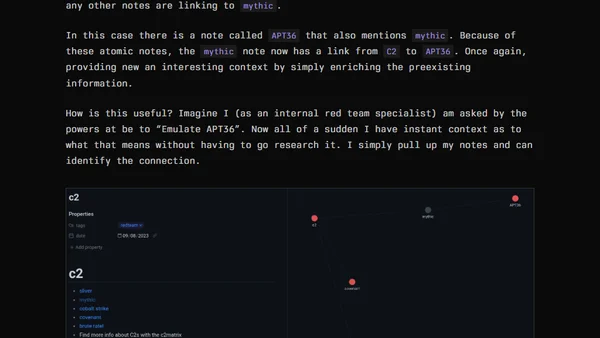
A security researcher shares a personal system for managing knowledge and taking effective notes for actionable cybersecurity learning and research.
A detailed analysis of memory unsafe programming languages, their security risks, and the types of software most affected by these vulnerabilities.