Finding a non-square mod p
Explains an algorithm for finding a non-square modulo a prime, with Python code and examples from cryptography.
Explains an algorithm for finding a non-square modulo a prime, with Python code and examples from cryptography.
Explains a zero-knowledge proof for verifying a product without revealing the numbers, using elliptic curves and pairings.
Explains how to construct a zero-knowledge proof to demonstrate knowledge of a discrete logarithm without revealing the secret value.
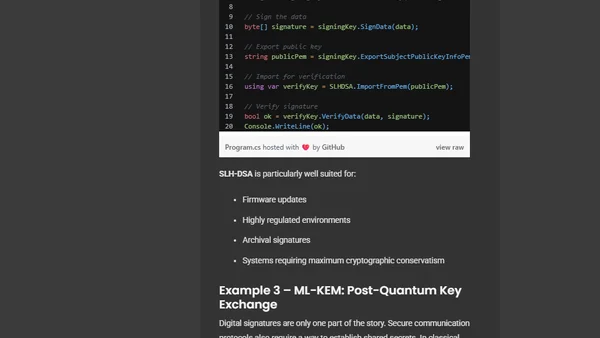
.NET 10 introduces built-in Post-Quantum Cryptography (PQC) APIs, enabling developers to adopt quantum-resistant algorithms for future security.
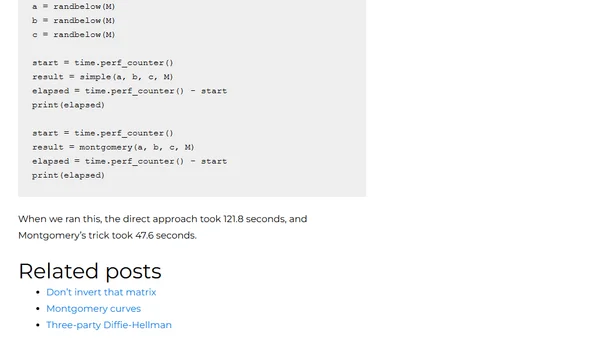
Explains Montgomery's trick for efficiently computing multiple modular inverses at once, with Python code examples and performance comparison.
Explores prime number chains like Cunningham chains and their application in the Primecoin cryptocurrency's proof-of-work system.
A simple, intuitive explanation of public key cryptography using analogies and a number game to explain how to prove a secret without revealing it.
LLVM 21 adds constant-time support to protect cryptographic code from timing attacks at the compiler level.
A summary of key developments in Go's cryptography ecosystem over the past year, including post-quantum key exchanges and security improvements.
A developer uses Claude Code to debug a complex bug in their Go implementation of the ML-DSA post-quantum cryptography algorithm.
A technical guide on generating private and public keys for the Nostr protocol locally using openssl and Secp256k1.
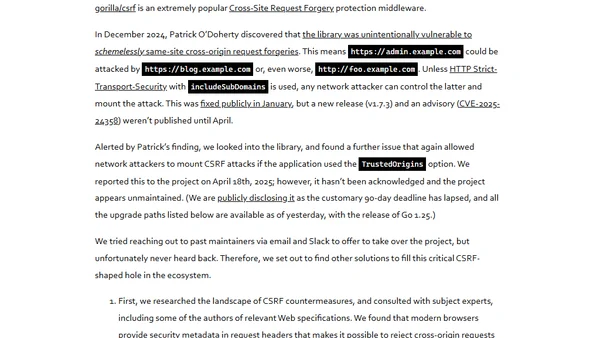
Geomys, a professional open source maintainer group, discusses taking over critical but unmaintained Go projects like bluemonday and gorilla/csrf as a 'maintainer of last resort'.
Overview of Himitsu 0.9, a secret storage manager for Linux, covering its new GTK4 prompter and Secret Service API integration.
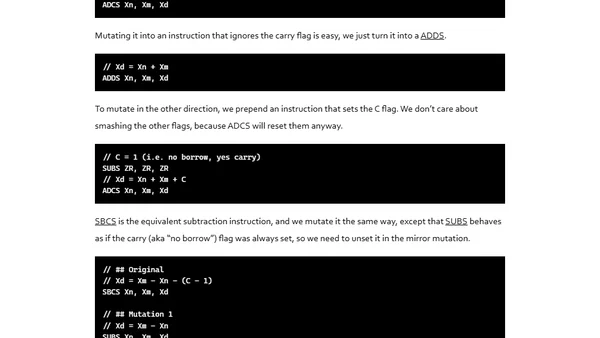
Introducing a mutation testing framework for Go assembly to improve test coverage of constant-time cryptographic code and prevent hidden bugs.
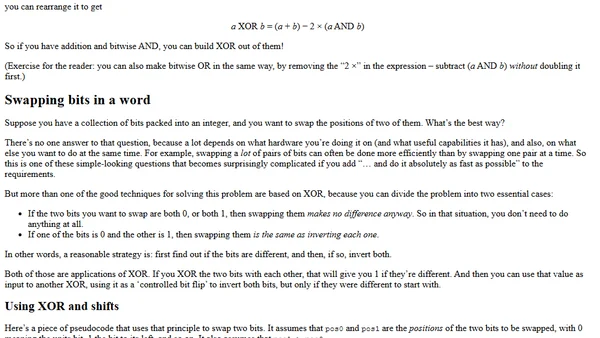
A comprehensive guide to the XOR operator, exploring its boolean logic, bitwise properties, mathematical concepts, and practical applications in computing.
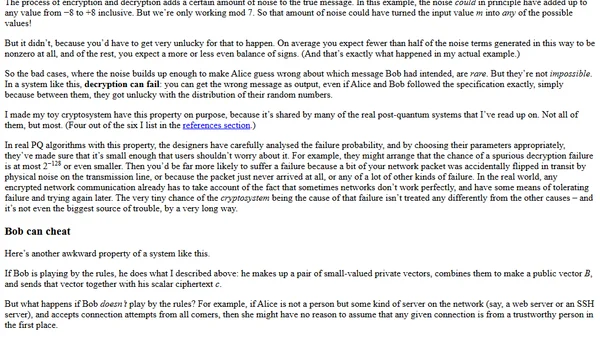
Explains post-quantum cryptography concepts, contrasting them with classical systems like RSA, and introduces a toy cryptosystem for educational purposes.
Explores the philosophical differences in cryptographic library design, focusing on algorithm inclusion, misuse-resistance, and user expectations.
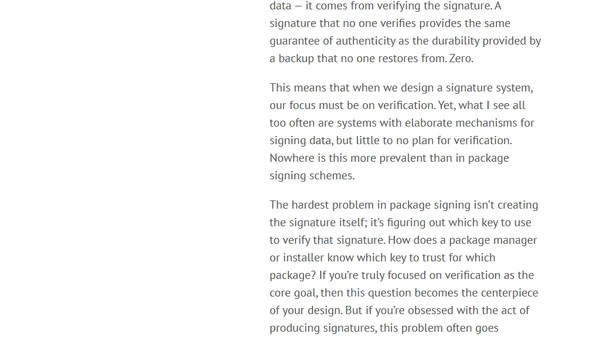
Argues that cryptographic signatures, like backups, are only valuable if they can be reliably verified, not just created.
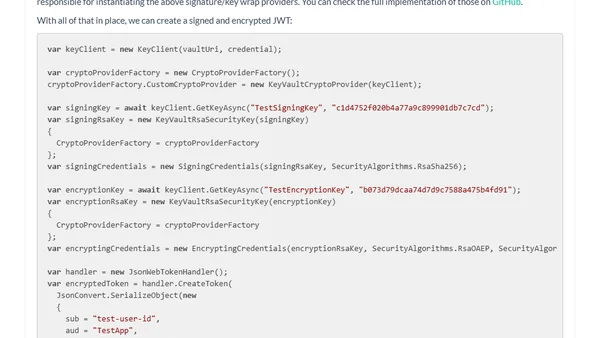
Explains how to use Azure Key Vault keys for signing and encrypting JSON Web Tokens (JWTs), including key rotation.
Explains the limitations of code signing for software security and introduces software provenance as a more robust alternative.