Relish: A new serialization format
Introducing Relish, a new binary serialization format for RPC and database use, designed with clean semantics and implemented in Rust.
Alex Gaynor is a software resilience engineer focused on building reliable, secure systems across government, industry, and open source. He writes about software security, serialization, benchmarks, and the economics of open-source infrastructure.
202 articles from this blog
Introducing Relish, a new binary serialization format for RPC and database use, designed with clean semantics and implemented in Rust.
Explores using legal 'motion to dismiss' concepts to evaluate software vulnerability reports against a project's threat model.
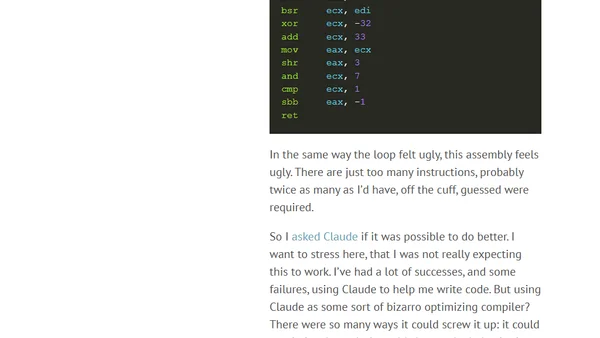
A technical deep dive into optimizing DER serialization in Rust, focusing on length encoding challenges and performance improvements.
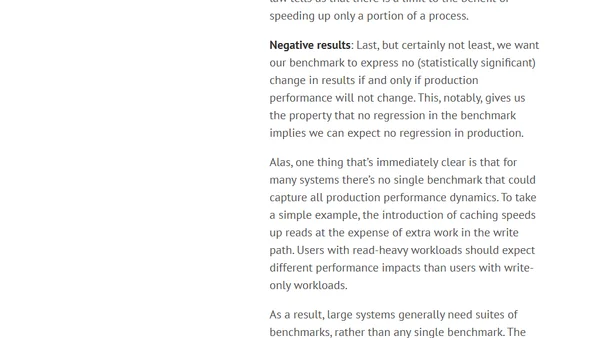
Explores the concept of software benchmarks as falsifiable hypotheses for predicting real-world system performance, not just speed tests.
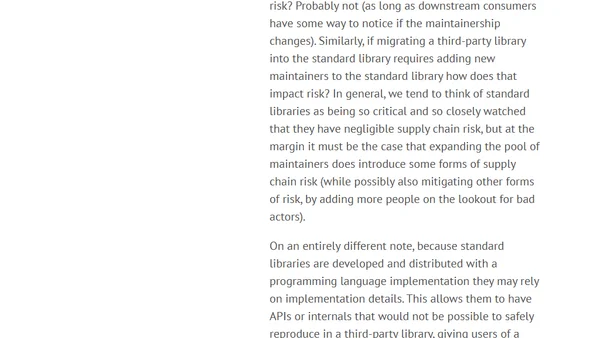
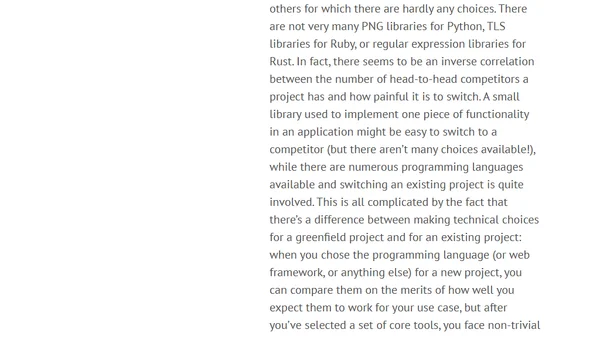
An analysis of standard libraries in programming languages, exploring their benefits, criticisms, and role in language ecosystems.
Analyzes why many open-source projects, especially volunteer-maintained ones, struggle to capture financial value despite creating substantial economic value.
Analyzes the negative long-term effects of Postel's Law on software ecosystems, arguing it creates a 'ratchet' of increasing specification deviance.
Analyzes the pros and cons of replacing GNU coreutils with a Rust implementation, focusing on security and performance arguments.
Explores the concept of 'generality' in AI models, using examples of ML failures and LLM inconsistencies to question how we assess their capabilities.
Analyzes the complex relationship between tech monopolies and workers, exploring antitrust law, labor monopsony, and output reduction effects.
Analyzes the business rationale behind the 'SSO Tax' and its negative impact on security, especially for small businesses.
An analysis of three common reasons why funding models for open source software projects often fail, based on the author's long-term experience.
Explores the role of IT security and other risk professionals in advising businesses, arguing for a normative approach to extreme risks.
Explores the philosophical differences in cryptographic library design, focusing on algorithm inclusion, misuse-resistance, and user expectations.
Argues that cryptographic signatures, like backups, are only valuable if they can be reliably verified, not just created.
Explores how memory safety affects sandboxing in complex systems like browsers, challenging the view that they are purely complementary security approaches.
Discusses strategies for improving memory safety in C++ codebases as a practical alternative to full migration to memory-safe languages.
A detailed analysis of memory unsafe programming languages, their security risks, and the types of software most affected by these vulnerabilities.
Explores a data race bug at the intersection of Python's buffer protocol and Rust's memory model, highlighting undefined behavior risks.
An analysis of semantic versioning (SemVer) and the practical challenges of maintaining true backwards compatibility in software APIs.