Motion to Dismiss for Failure to State a Vulnerability
Explores using legal 'motion to dismiss' concepts to evaluate software vulnerability reports against a project's threat model.
Explores using legal 'motion to dismiss' concepts to evaluate software vulnerability reports against a project's threat model.
A framework for evaluating security threats and risks in Model Context Protocol (MCP) implementations, based on recent incidents.
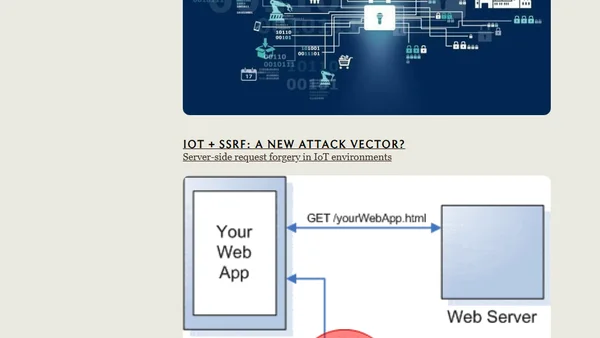
A comprehensive index of cybersecurity frameworks, threat modeling systems, assessment methodologies, and web application security principles from decades of infosec experience.
Using Python's pytm framework to threat model the security flaws in the fictional systems of Jurassic Park.
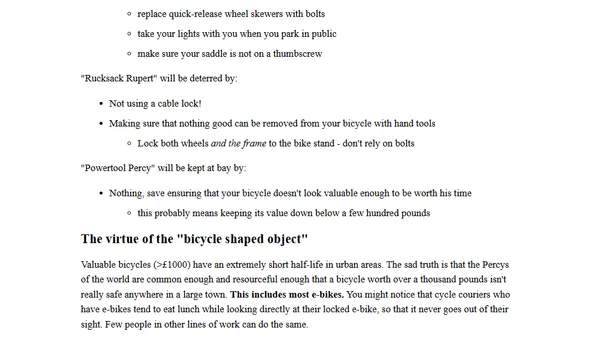
A threat modeling case study using bicycle theft to illustrate security principles applicable to IT systems.
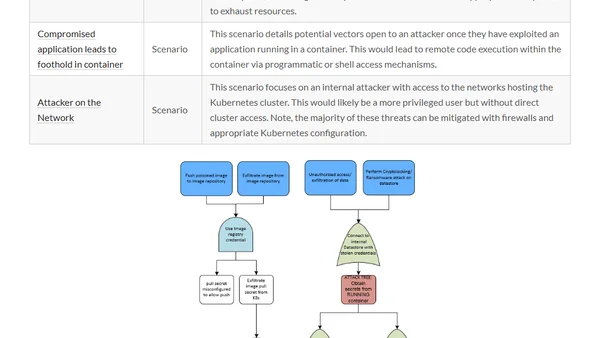
A summary of three major Kubernetes threat modeling initiatives to help security professionals secure their production clusters.
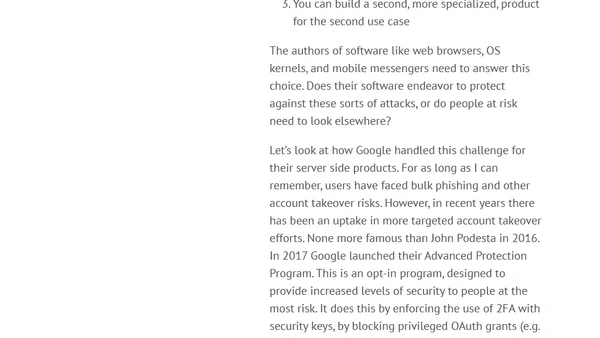
Explores the challenge of building safety-critical software for high-risk users like activists, contrasting it with mainstream security needs.
A framework for categorizing security engineering work into four key buckets: prevention, detection, damage reduction, and work generation.
An introduction to threat modeling, a security technique for identifying assets, attack vectors, and attackers to build better system defenses.