the last couple years in v8's garbage collector
An analysis of recent developments in the V8 JavaScript engine's garbage collector, focusing on memory safety, Oilpan, and multi-threading support.
An analysis of recent developments in the V8 JavaScript engine's garbage collector, focusing on memory safety, Oilpan, and multi-threading support.
Chrome, Firefox, and WebKit plan to remove XSLT from browsers by 2026, citing significant security risks in the aging codebase.
Analysis of 2024/2025 open source supply chain compromises, categorizing root causes like control handoff, phishing, and CI/CD vulnerabilities.
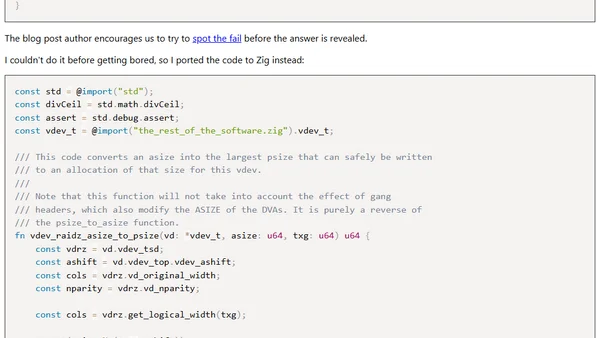
Analyzing a critical OpenZFS bug by porting the flawed C code to Zig, demonstrating how Zig's compiler catches the error.
Analyzes the pros and cons of replacing GNU coreutils with a Rust implementation, focusing on security and performance arguments.
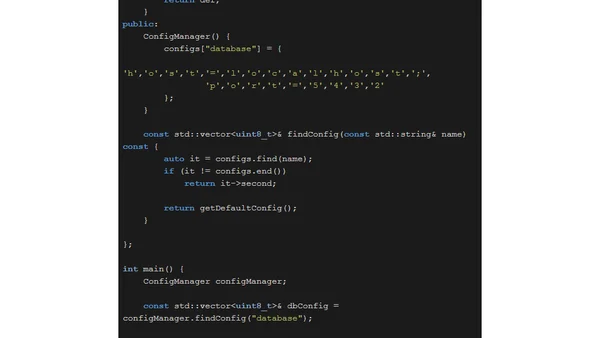
Explores C++26's new safety features to prevent dangling references in a configuration manager, with code examples and fixes.
An article clarifying common misconceptions about the 'unsafe' keyword in Rust, explaining that it does not disable the borrow checker.
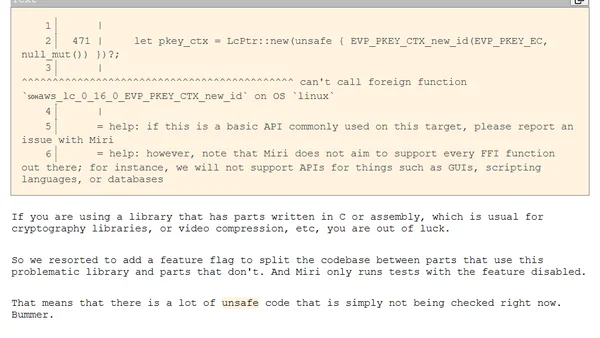
A developer shares key insights and practical lessons from a successful, incremental rewrite of a C++ codebase to Rust.
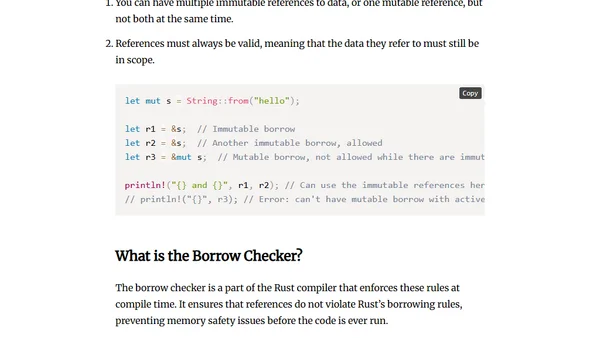
An introductory guide to Rust, covering its key features like memory safety, ownership, and setup for developers new to the language.
Explores how memory safety affects sandboxing in complex systems like browsers, challenging the view that they are purely complementary security approaches.
Discusses strategies for improving memory safety in C++ codebases as a practical alternative to full migration to memory-safe languages.
A detailed analysis of memory unsafe programming languages, their security risks, and the types of software most affected by these vulnerabilities.
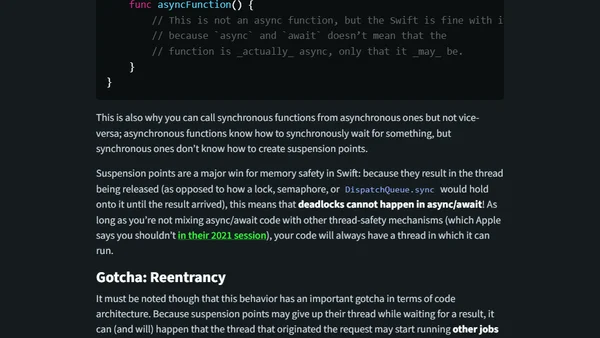
A deep dive into the internal workings, history, and implementation of async/await in Swift, exploring its design and gotchas.
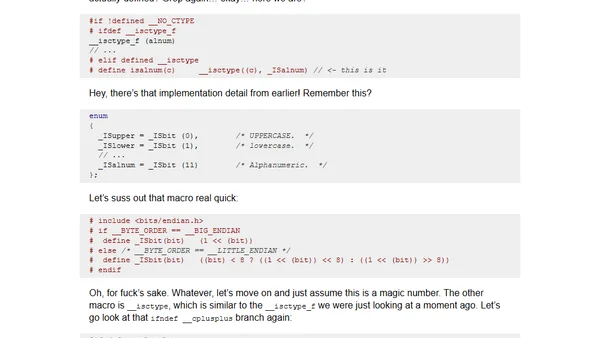
A developer compares musl libc and glibc implementations after a segfault bug in scdoc, highlighting differences in isalnum behavior.
Analysis of empirical data showing memory unsafety causes 65%+ of security vulnerabilities in large C/C++ codebases like Android, Chrome, and Linux.
Outlines key research areas needed to accelerate the adoption of memory-safe programming languages like Rust and improve migration from unsafe languages like C/C++.
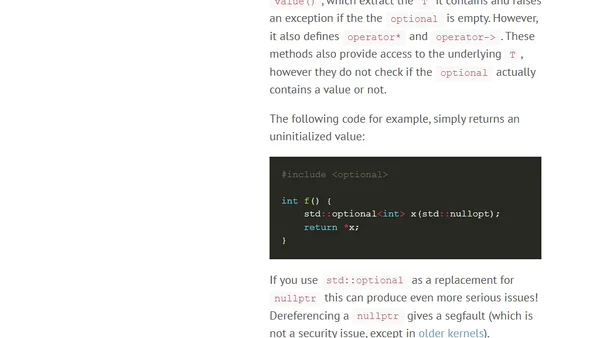
Argues that modern C++ idioms like smart pointers and string_view are insufficient to prevent memory safety vulnerabilities, advocating for memory-safe languages.
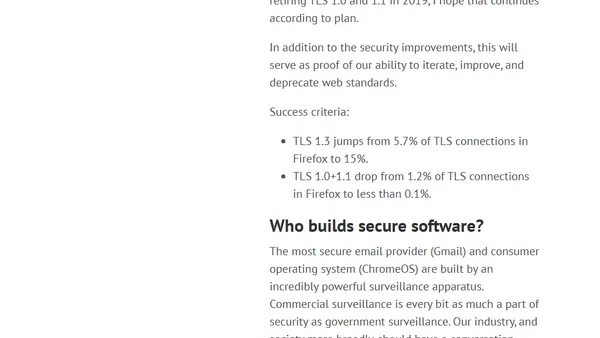
A security expert's wish list for 2019, focusing on Rust adoption, security keys, and TLS 1.3 deployment to improve computer security.
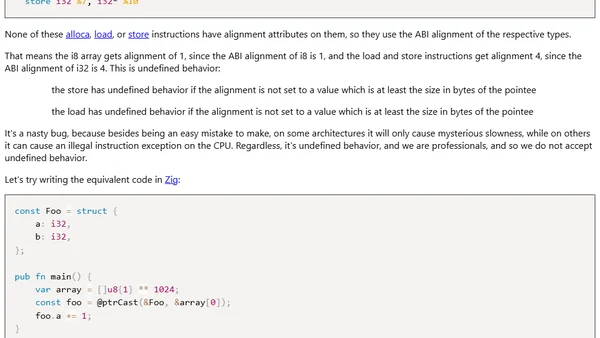
Analyzes undefined behavior in unsafe Rust code when transmuting pointers, comparing it to Zig's safety guarantees.
Argues that memory unsafety is a widespread, unnamed vulnerability causing thousands of bugs, and advocates for adopting memory-safe languages like Rust.