Authentication in JavaScript & TypeScript
A tutorial on building a custom, session-based authentication system in JavaScript and TypeScript, covering secure password handling and session management.
A tutorial on building a custom, session-based authentication system in JavaScript and TypeScript, covering secure password handling and session management.
A speaker shares insights from a DevOps meetup, focusing on key security features introduced in Kubernetes 1.31.
Explores the philosophical differences in cryptographic library design, focusing on algorithm inclusion, misuse-resistance, and user expectations.

A guide to implementing fine-grained permissions for SQL Server Extended Events to enforce the Principle of Least Privilege with role separation examples.

An analysis of AWS EKS Pod Identity, comparing it to IRSA, explaining its benefits, and discussing why the author's company hasn't adopted it yet.
Argues that cryptographic signatures, like backups, are only valuable if they can be reliably verified, not just created.
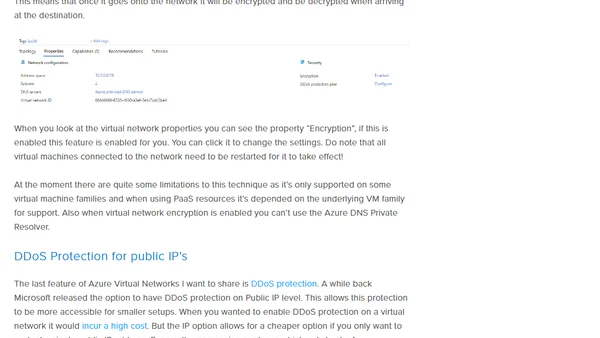
Explores new Azure network security features like default outbound access removal and virtual network encryption for a Zero Trust approach.
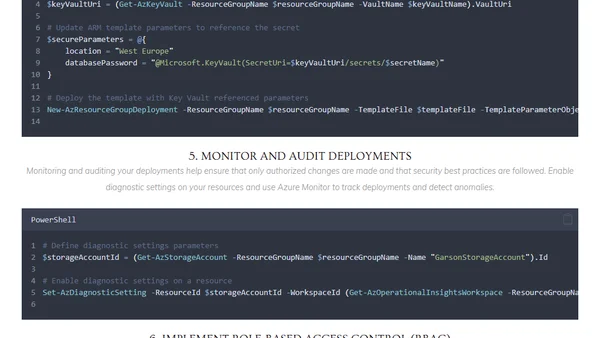
Explores best practices for securing Azure ARM templates and using PowerShell to automate secure Infrastructure as Code deployments.
Explores how memory safety affects sandboxing in complex systems like browsers, challenging the view that they are purely complementary security approaches.
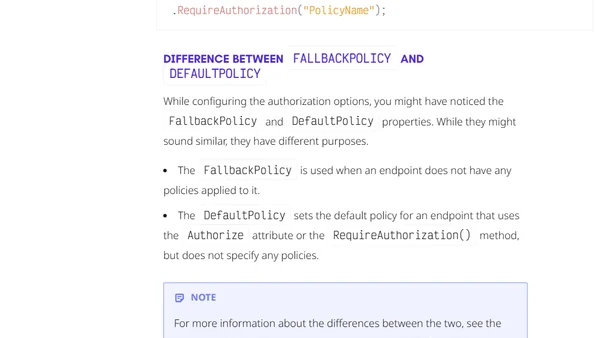
A developer shares lessons learned and pitfalls to avoid when implementing policy-based authorization in .NET applications.

A former Azure SQL security engineer outlines seven key improvements needed for access control and security in SQL Server and Azure SQL.
Discussion on alternative app stores for iOS, their impact on developer workflows, code signing requirements, and preparing for new OS versions.
A technical guide on implementing DNSSEC using Azure's private preview feature, detailing the PowerShell command and its significance for security compliance.
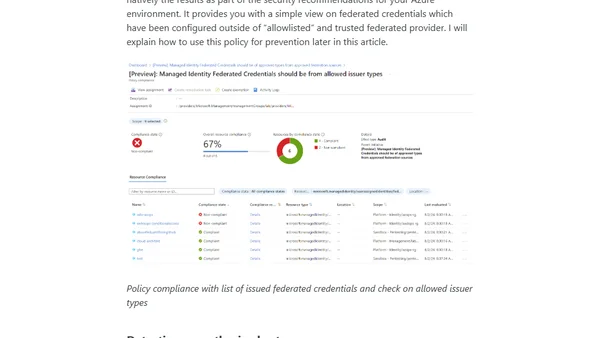
Explains security risks and attack scenarios for Managed Identities using Federated Credentials in Azure, focusing on privilege requirements and abuse prevention.
Analysis of W3C TAG's response to Google delaying third-party cookie removal, discussing privacy, ad tech, and web standards.
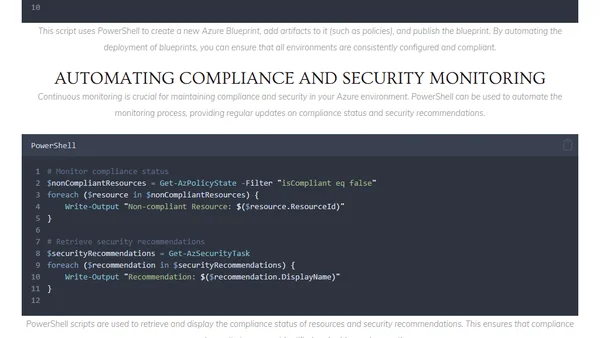
How to use PowerShell to automate compliance and security tasks in Microsoft Azure, including policy management and security monitoring.
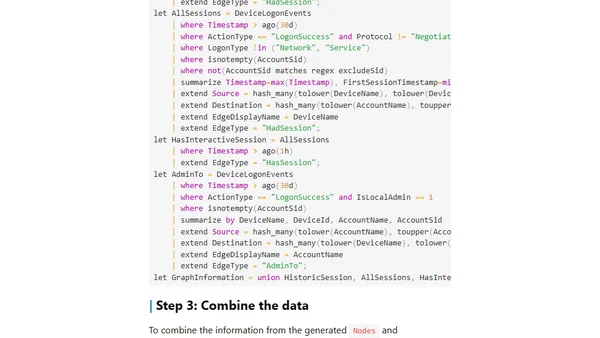
Explains how to use KQL Graph semantics in Microsoft security tools to identify lateral movement paths between users, computers, and groups.
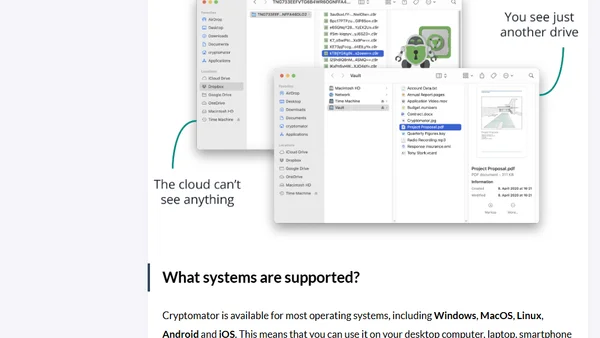
Explains how Cryptomator, a free open-source tool, provides end-to-end encryption for files stored in cloud services like Google Drive or Dropbox.
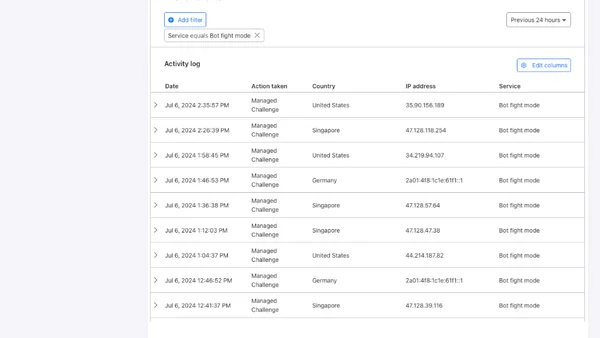
Cloudflare now offers a simple setting to block AI bots from scraping your website, available even on free plans.
A guide on how to permanently remove a file containing sensitive data (like a password) from your entire Git repository history using a specific command.