Storage Account: You do not have permissions to list the data using your user account with Entra ID
Explains why being an Azure Storage Account Owner doesn't grant data access and how to assign the correct Storage Data roles.
Explains why being an Azure Storage Account Owner doesn't grant data access and how to assign the correct Storage Data roles.
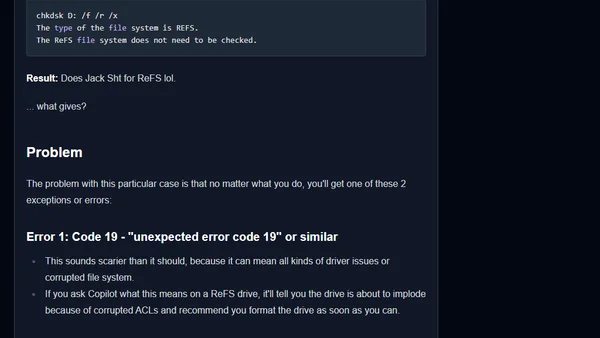
A technical guide diagnosing and attempting to fix a ReFS Dev Drive on Windows that has become write-protected due to system updates or policies.
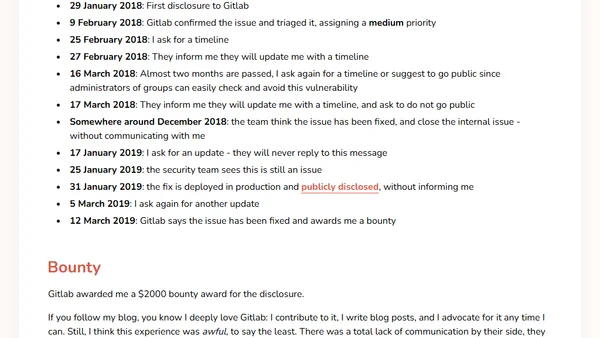
A security researcher details a GitLab access control vulnerability, its disclosure timeline, and the communication issues with GitLab's security team.
Developer shares their new role as a Developer Advocate at Pomerium, a Zero Trust access control platform, and discusses the company's open-source approach.
Explains how to implement access control and security for Apache Iceberg tables at the file, engine, and catalog levels.

A former Azure SQL security engineer outlines seven key improvements needed for access control and security in SQL Server and Azure SQL.
Analysis of the NSA and CISA's top 10 cybersecurity misconfigurations, offering insights for IT and business leaders on common network security risks.
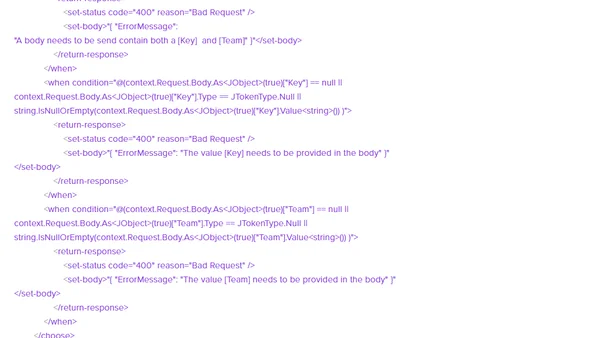
Using Azure API Management to control API access and validate parameters per team, securing an Azure Function for DevOps agent management.
Azure Monitor Log Alerts now support Managed Identity for secure query execution, enabling integration with Azure Data Explorer.
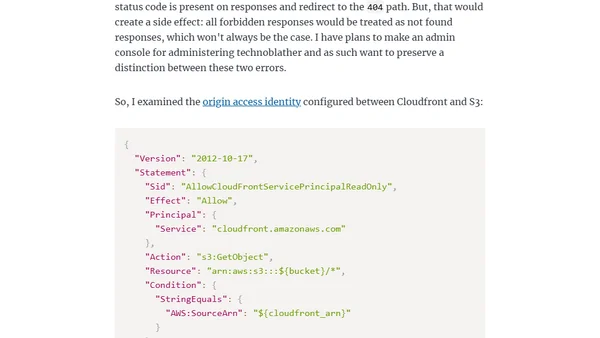
A technical guide on fixing S3 bucket 403 errors to show proper 404 pages in Cloudfront without making the bucket public.
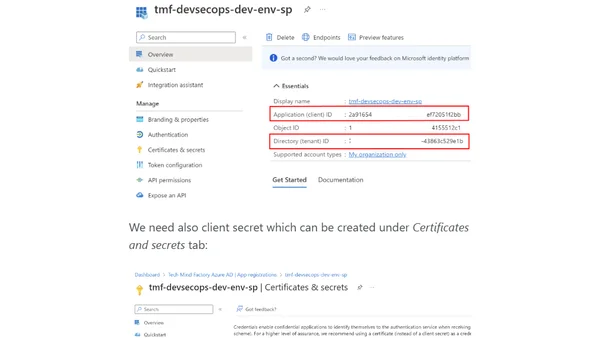
Explains how Azure AD and RBAC control access to Azure DevOps, GitHub, and Azure resources as part of DevSecOps identity management.
A developer's perspective on the challenges of implementing authorization (authz) in software, balancing minimal effort with security needs.
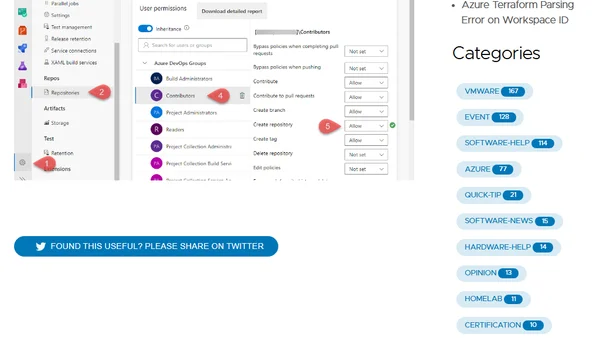
Troubleshooting guide for Azure DevOps Contributors encountering TF401027 error when trying to create a new repository.
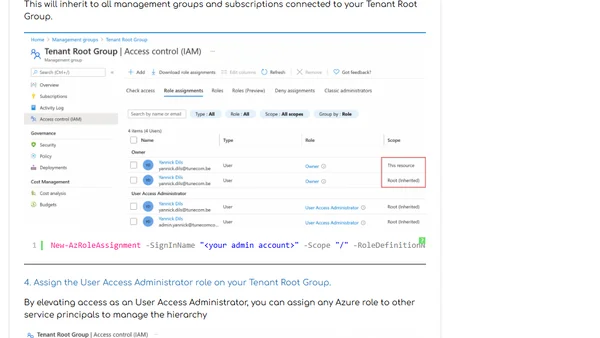
A guide to regaining administrative access to your Azure Root Management Group after accidentally locking yourself out.

Explains the 'Need-to-know' security principle for SQL Server and Azure SQL, detailing access control methods and implementation scenarios.
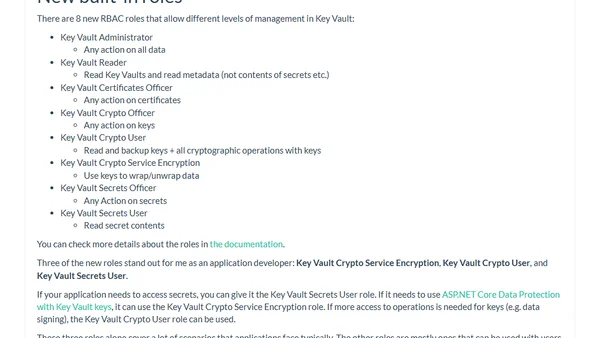
Explains how to use Azure Role-Based Access Control (RBAC) with Azure Key Vault, including enabling it and the new built-in roles.
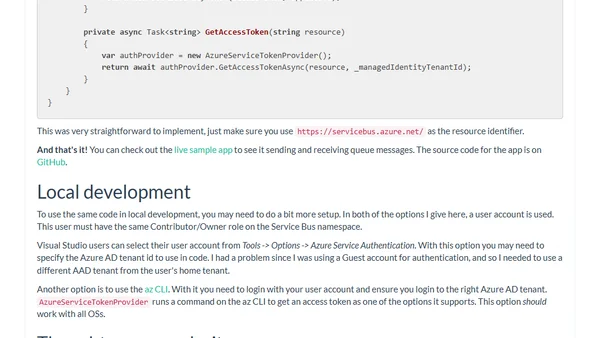
A technical guide on using Azure Managed Identities to authenticate and access Azure Service Bus, eliminating the need for stored connection strings.
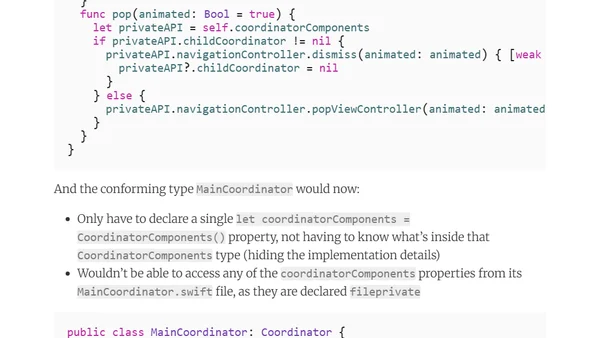
Explains a workaround for creating private properties in Swift protocols to hide implementation details from conforming types.
Guide on granting non-admin users read-only access to Service Endpoints in Visual Studio Team Services (VSTS) for secure deployments.
A guide to implementing Access Control List (ACL) authorization using the Gate system in Laravel 5.1.