A vulnerability by any other name
Argues that memory unsafety is a widespread, unnamed vulnerability causing thousands of bugs, and advocates for adopting memory-safe languages like Rust.
Alex Gaynor is a software resilience engineer focused on building reliable, secure systems across government, industry, and open source. He writes about software security, serialization, benchmarks, and the economics of open-source infrastructure.
202 articles from this blog
Argues that memory unsafety is a widespread, unnamed vulnerability causing thousands of bugs, and advocates for adopting memory-safe languages like Rust.
A technical critique of Deputy AG Rosenstein's speeches linking encryption to cybersecurity threats, arguing his position misrepresents the role of encryption in major breaches.
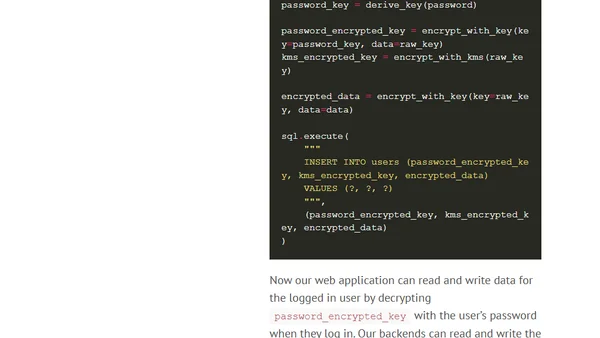
Analyzes the Apache Struts CVE-2017-5638 vulnerability, using the Equifax breach as a case study to explore architectural resilience against RCE attacks.
A framework for categorizing security engineering work into four key buckets: prevention, detection, damage reduction, and work generation.
Explains why forward secrecy is crucial for modern encryption, contrasting GPG's long-term key model with the Signal Protocol's ephemeral keys.
Explains Certificate Transparency for server operators, its importance for HTTPS security, and tools like crt.sh to verify certificate logs.
A developer tracks HTTP vs HTTPS requests for a year, highlighting major websites still using insecure HTTP and advocating for HTTPS adoption.
Discusses the importance of cryptographic safety factors, using SHA1's vulnerabilities and Feynman's Challenger report as analogies.
A software engineer with extensive experience in open source, security, and multiple languages announces they are seeking a new role focused on impactful information security work.
A developer's initial experience using Google's OSS-Fuzz project to perform large-scale fuzz testing on the open-source libyaml library.
An introduction to threat modeling, a security technique for identifying assets, attack vectors, and attackers to build better system defenses.

Analysis of a cryptographic vulnerability in the Beaker Python library's session encryption due to nonce reuse in AES-CTR mode.
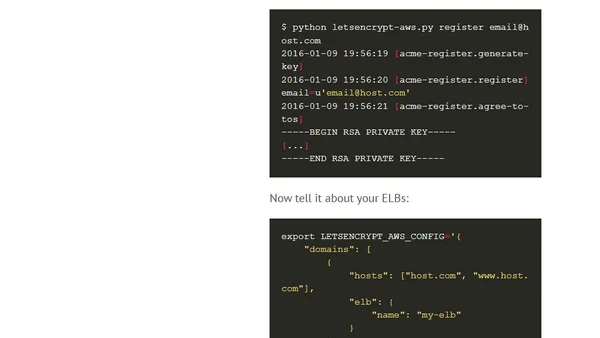
Introducing letsencrypt-aws, a tool to automate Let's Encrypt SSL certificate issuance and renewal for AWS infrastructure like ELBs.
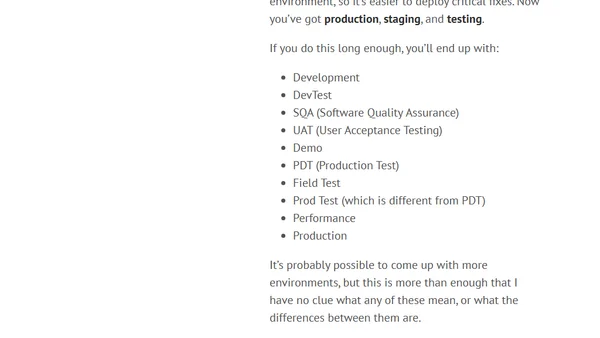
A critique of complex multi-environment deployment workflows, arguing they create more problems than they solve.
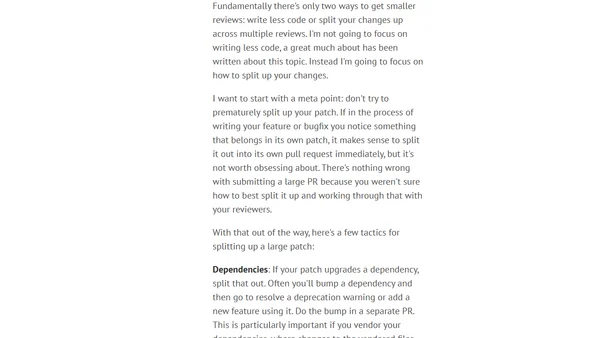
Explains why smaller code reviews are more effective and offers practical strategies for splitting large patches into manageable pieces.
Highlights five key projects advancing security: U2F, Let's Encrypt, Rust, X25519/Ed25519, and Chromebooks.
Discusses the benefits and challenges of adding telemetry to open source libraries to improve maintenance decisions.
A developer's experience with Rust's modern tooling, highlighting the Cargo build system and its benefits for dependency management and deployment.
Practical advice for enhancing company security, covering password storage, SSH access, network encryption, patching, and developer education.
A guide to improving performance, scalability, and cost for web applications, covering CDNs, sessions, load balancing, and object storage.