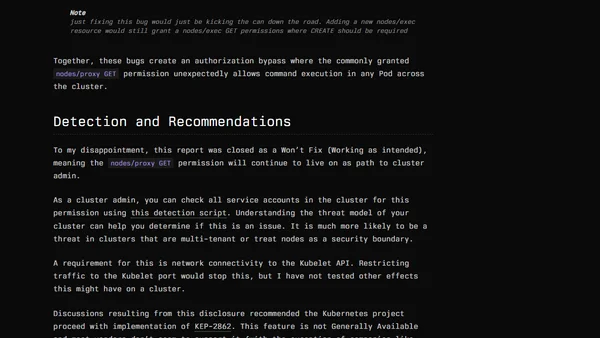
Kubernetes Remote Code Execution Via Nodes/Proxy GET Permission
Explains how nodes/proxy GET permissions in Kubernetes can be exploited for remote code execution, detailing the vulnerability and affected Helm charts.
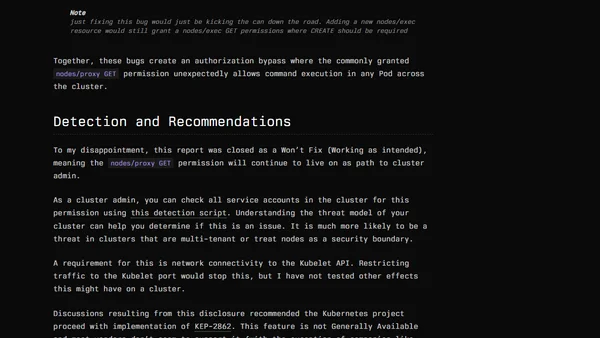
Explains how nodes/proxy GET permissions in Kubernetes can be exploited for remote code execution, detailing the vulnerability and affected Helm charts.
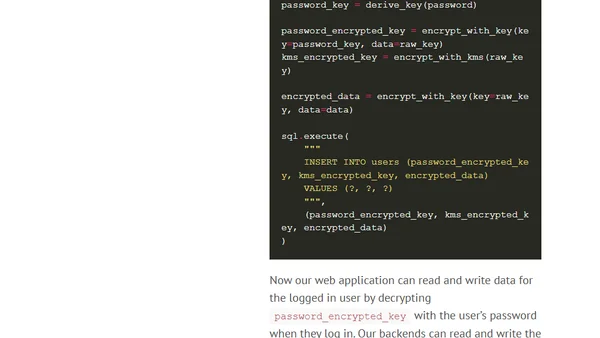
Analyzes the Apache Struts CVE-2017-5638 vulnerability, using the Equifax breach as a case study to explore architectural resilience against RCE attacks.

Discusses critical SQL Server security patches (MS15-058) and emphasizes the importance of following security best practices like least-privilege access.