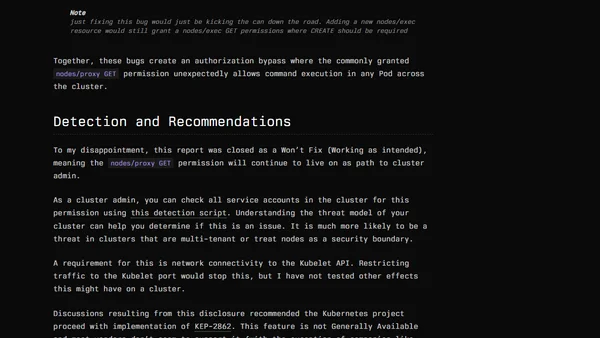
Kubernetes Remote Code Execution Via Nodes/Proxy GET Permission
Explains how nodes/proxy GET permissions in Kubernetes can be exploited for remote code execution, detailing the vulnerability and affected Helm charts.
Explains how nodes/proxy GET permissions in Kubernetes can be exploited for remote code execution, detailing the vulnerability and affected Helm charts.
A recap of Cloud Native Rejekts NA 2025, highlighting key talks on Kubernetes security, AI infrastructure, and platform engineering.
A tech professional outlines their 2025 focus on Platform Security, Kubernetes, Azure Security, and Cloud Vulnerability Research, and invites collaboration.

A guide to using the open-source security tool Falco for dynamic security monitoring and threat detection in AWS EKS Kubernetes clusters.