Why software ends up complex
Explores why software becomes complex over time, focusing on the additive nature of feature requests and the lack of a strong constituency for simplicity.
Alex Gaynor is a software resilience engineer focused on building reliable, secure systems across government, industry, and open source. He writes about software security, serialization, benchmarks, and the economics of open-source infrastructure.
202 articles from this blog
Explores why software becomes complex over time, focusing on the additive nature of feature requests and the lack of a strong constituency for simplicity.
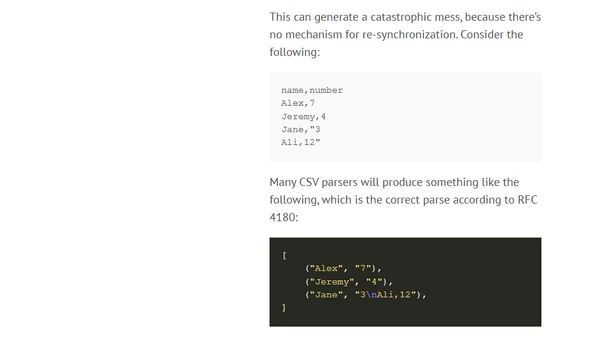
An analysis of the CSV data format, covering its advantages, drawbacks, and common parsing pitfalls in data processing.
Analysis of empirical data showing memory unsafety causes 65%+ of security vulnerabilities in large C/C++ codebases like Android, Chrome, and Linux.
A reflection on the personal and professional benefits of being an open source maintainer, framed in the spirit of the Passover song 'Dayenu'.
Discusses the challenges of scaling software development over time, emphasizing the need for automated enforcement of code properties as projects grow.
A review of 2019 security predictions, covering progress on Rust adoption, WebAuthn security keys, and TLS 1.3 deployment.
Explores the challenge of building safety-critical software for high-risk users like activists, contrasting it with mainstream security needs.
Outlines key research areas needed to accelerate the adoption of memory-safe programming languages like Rust and improve migration from unsafe languages like C/C++.
Explains memory unsafety in programming languages, its security risks (out-of-bounds reads/writes, use-after-free), and contrasts unsafe languages like C/C++ with safe ones.
The article argues for the importance of developing code reading as a critical skill for software engineers, alongside writing code.
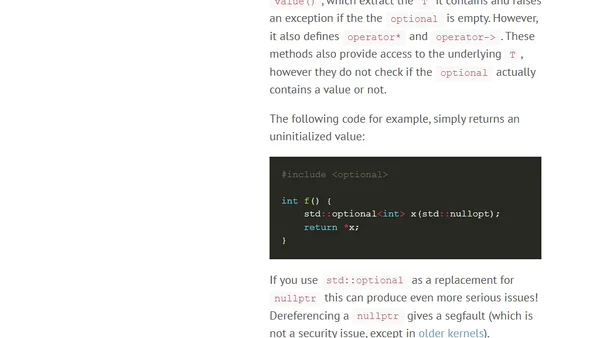
Argues that modern C++ idioms like smart pointers and string_view are insufficient to prevent memory safety vulnerabilities, advocating for memory-safe languages.
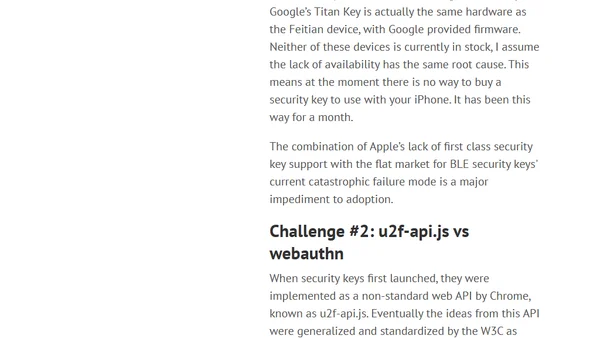
Analyzes technical and market challenges hindering widespread adoption of security keys, focusing on iOS limitations and API fragmentation.
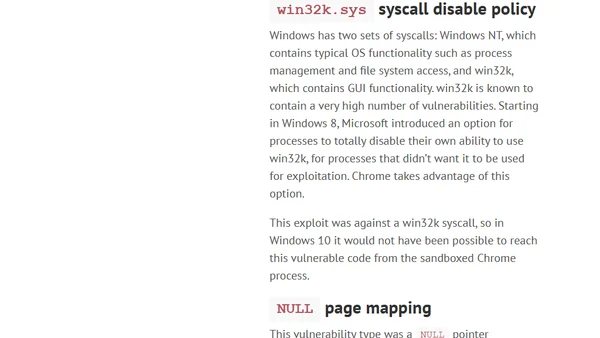
Analysis of a Chrome/Windows exploit chain, explaining why Windows 10 mitigations make it harder to exploit than on Windows 7.
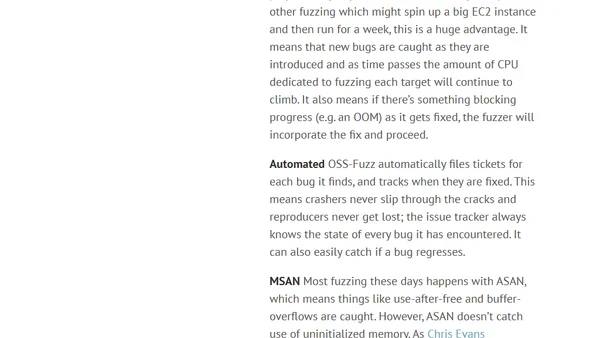
Analysis of fuzzing ImageMagick and GraphicsMagick with OSS-Fuzz, revealing hundreds of security bugs despite prior audits.
A security expert's wish list for 2019, focusing on Rust adoption, security keys, and TLS 1.3 deployment to improve computer security.
The article argues for optimizing code for auditability to make security vulnerabilities easier to spot, using cryptography as a key example.
Challenges the common security truism that defenders must be perfect, arguing for a more realistic, economics-based approach to defense.
A former US Digital Service engineer shares two key lessons on government tech impact and the value of meaningful work, even when it risks burnout.
Analyzes the debate around zero-day vulnerability disclosure, arguing that lack of public evidence doesn't mean exploits aren't being used by stealthy attackers.
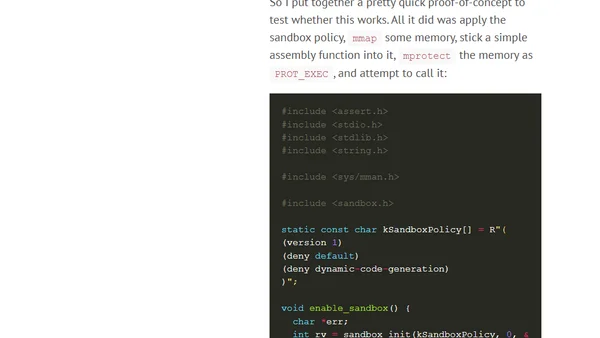
A Firefox security engineer investigates exploit mitigations like Arbitrary Code Guard (ACG) and its feasibility for macOS, focusing on dynamic code generation restrictions.