How to Securely Store Secrets in Environment Variables
A guide on protecting API keys and secrets from malware by avoiding environment variables and using a password manager with CLI integration.
A guide on protecting API keys and secrets from malware by avoiding environment variables and using a password manager with CLI integration.
Explores the 'Normalization of Deviance' concept in AI safety, warning against complacency with LLM vulnerabilities like prompt injection.

Analysis of Microsoft's Secure Future Initiative report, emphasizing trust as a core architectural dimension and the risks of timing debt in hybrid infrastructure.

Analyzes the pros and cons of renaming the built-in SQL Server 'sa' account as a security measure against brute-force attacks.
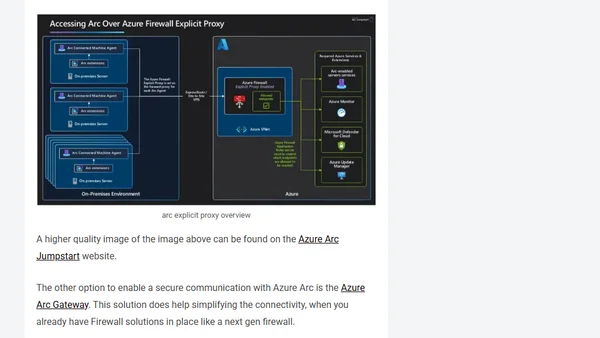
Explains why traditional ESAE security for Tier 0 assets is outdated and details a modern approach using Azure Arc with dedicated subscriptions and tightened controls.
Fixing YouTube embed error 153 by adjusting Django's Referrer-Policy header from same-origin to strict-origin-when-cross-origin.

Microsoft Intune's Multi Admin Approval feature now secures critical device actions like wipe, retire, and delete, requiring a second admin's approval.
A summary of key developments in Go's cryptography ecosystem over the past year, including post-quantum key exchanges and security improvements.
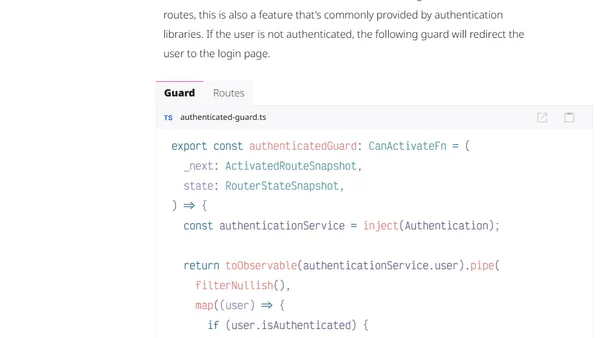
Explains how to implement secure cookie-based authentication in an Angular frontend, comparing it to the Authorization Code flow with PKCE.
Explains Docker Hub's new immutable tags feature, covering their benefits for reproducibility and how to configure them per repository.
Introduces the Geomys Standard of Care, a professional framework for secure and reliable open-source software maintenance.
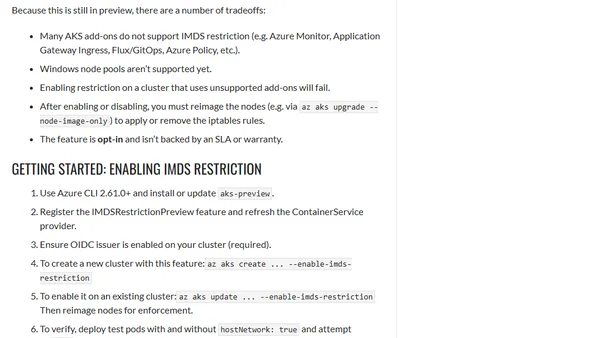
Microsoft introduces a preview feature for AKS to block pod access to the Azure Instance Metadata Service (IMDS), enhancing cluster security.
Analysis of 2024/2025 open source supply chain compromises, categorizing root causes like control handoff, phishing, and CI/CD vulnerabilities.
Analysis of a security attack exploiting toxic flows in the Model Context Protocol (MCP) to target Cursor IDE users via Jira tickets.
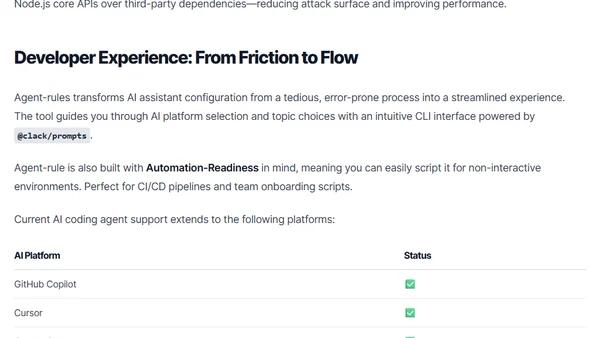
Introduces agent-rules, an open-source CLI tool that standardizes security and coding rules across AI coding assistants like GitHub Copilot and Cursor.
A guide to securing Azure Logic Apps HTTP triggers by replacing SAS tokens with OAuth authorization policies and Azure AD authentication.
A critique of JavaScript's dependency management after a major supply-chain attack, arguing for systemic change but predicting stagnation.
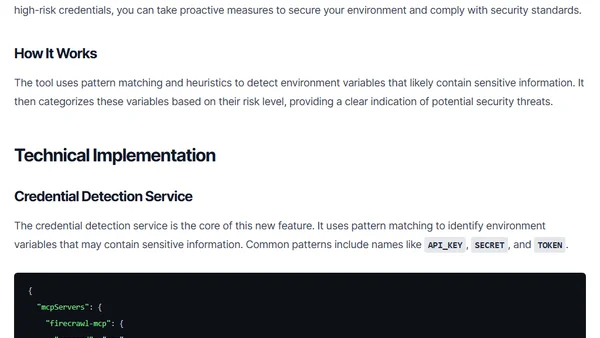
The ls-mcp tool update adds a security feature to detect and assess the risk of credentials stored in environment variables within MCP server configurations.
A guide to implementing Zero Trust security principles within Microsoft Azure, covering identity management, network segmentation, and continuous monitoring.
Explains the security risks of community-developed MCP servers and how to centrally manage and secure them using an MCP Gateway.