Service
A reflection on the ethical responsibilities of open source maintainers, especially regarding security and user dependency, beyond the 'volunteer' excuse.
A reflection on the ethical responsibilities of open source maintainers, especially regarding security and user dependency, beyond the 'volunteer' excuse.

Explains new SQL Server 2014 permissions like IMPERSONATE ANY LOGIN and how they interact with CONTROL SERVER for security and privilege escalation.
A blogger clarifies that Skype's unencrypted local database is not a security vulnerability, as it's protected by system-level access controls.
A practical guide on the essential and non-essential elements for building a successful web application, emphasizing simplicity and core problem-solving.
A blog post explaining the Heartbleed OpenSSL vulnerability and providing Python scripts to test websites for it.
A technical talk on the challenges and proper implementation of TLS/SSL for secure communications, presented at multiple Python conferences.
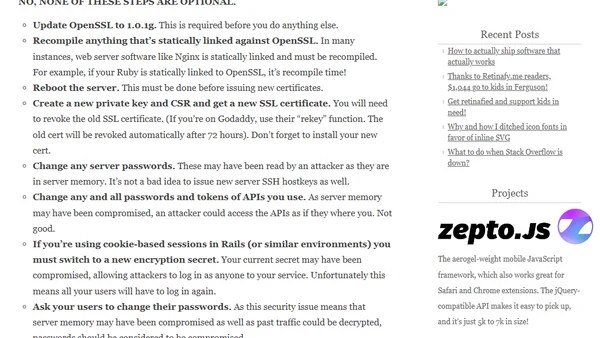
A concise, urgent guide for sysadmins on the mandatory steps to fix the critical Heartbleed OpenSSL vulnerability and secure web servers.
Explains the April 7 web security vulnerability, its impact on major sites, and provides steps for users to protect their accounts.

Explores the security implications of disabling SQL Server logins and denying permissions, focusing on how impersonation remains possible.
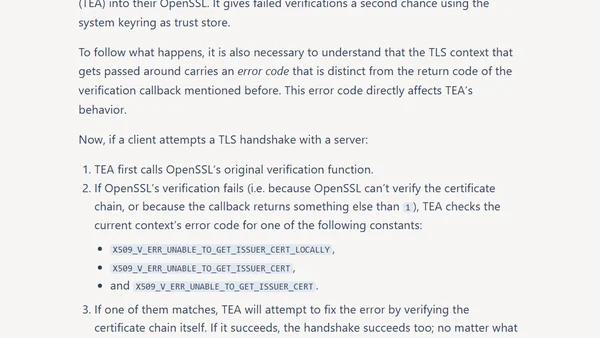
Apple's modified OpenSSL in macOS overrides verification failures and breaks the standard verification callback, potentially creating security risks.
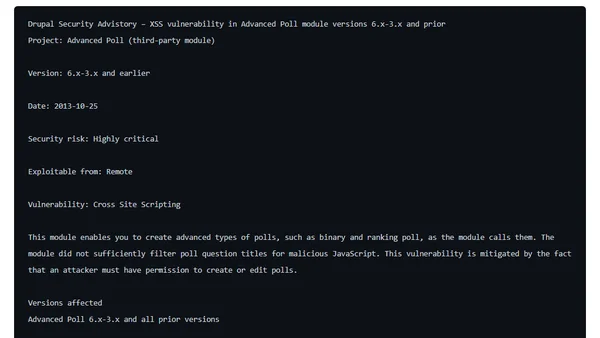
Details an XSS vulnerability in the Drupal Advanced Poll module (6.x-3.x and prior), including patch and mitigation.
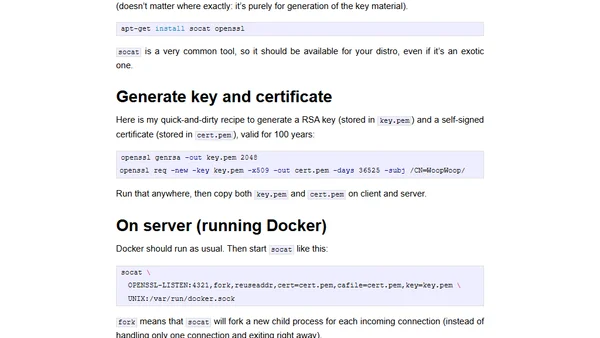
A guide to securing the Docker API by using SSL certificates and socat for encrypted, authenticated remote connections.
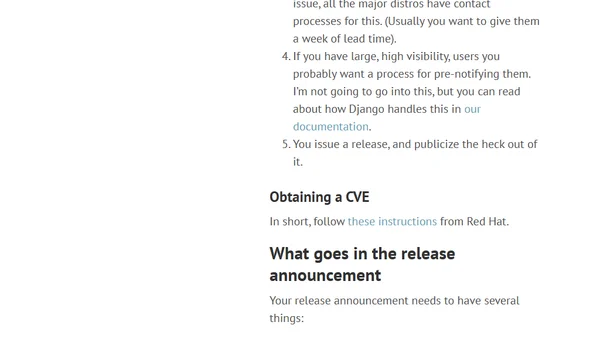
A guide outlining a responsible security vulnerability disclosure and patching process for open source software projects.

A security-focused session at SQL Rally Amsterdam demonstrating privilege elevation and DoS attacks via SQL Injection on SQL Server.
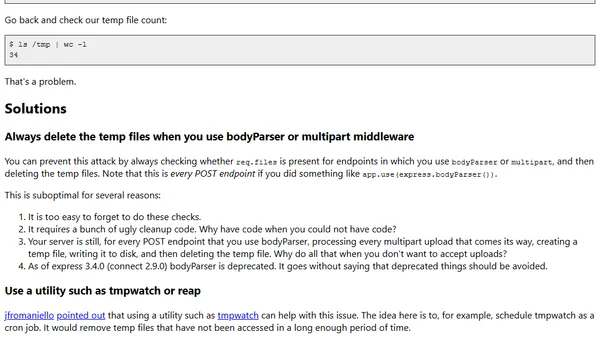
Explains a security vulnerability in Express.js's bodyParser middleware and provides safer alternatives for handling file uploads.
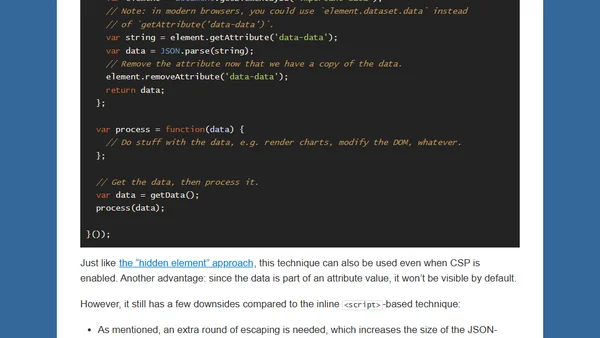
Explains how to pass server-generated JSON data to the front-end when Content Security Policy (CSP) blocks inline scripts, comparing performance impacts.

Explores SQL Server privilege escalation from CONTROL SERVER to sysadmin, debunking myths and comparing to Oracle's security model.
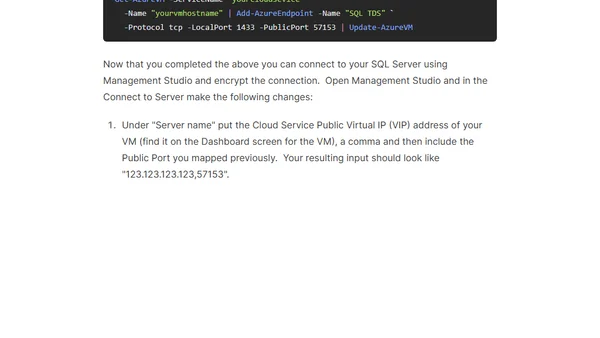
Guide to securely connect SQL Server Management Studio to an Azure IaaS SQL Server instance by configuring endpoints and enabling encrypted connections.
A humorous proof-of-concept exploit using HTML5 localStorage to fill a user's hard disk, highlighting browser security flaws.

A user investigates why Google search results for 'stackoverflow' incorrectly linked to a US government website, revealing a web developer's redirect error.