Is Privacy Dead?
A personal reflection on the trade-offs between convenience and privacy in an era of AI, IoT, and pervasive data collection.
A personal reflection on the trade-offs between convenience and privacy in an era of AI, IoT, and pervasive data collection.
Discusses the inevitability of website breaches, lists major hacks, and explains how to assess your risk and prepare for security incidents.
An introduction to threat modeling, a security technique for identifying assets, attack vectors, and attackers to build better system defenses.
Analysis of Kenya's proposed ICT law amendments, focusing on cybersecurity, electronic transactions, and potential issues in the draft regulations.
Essential security practices for freelance developers, covering device locking, password management, and multi-factor authentication.
A cautionary analysis of the Code Spaces hack, explaining how similar cloud security breaches can happen on AWS, Azure, or any host, and outlining basic mitigation steps.
A tech news roundup covering a wireless medical chip breakthrough, the 40th anniversary of the Rubik's Cube, and issues in web payments and cybersecurity.
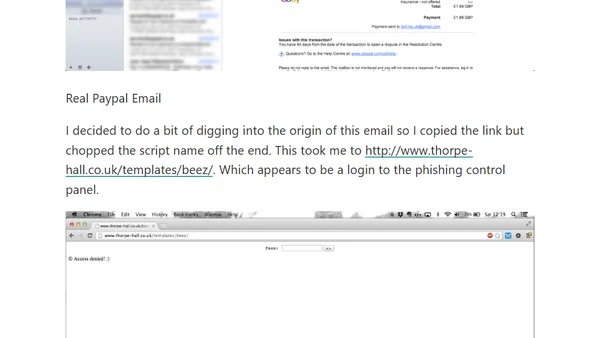
A detailed analysis of a convincing PayPal phishing email, including how to spot the fakes and the discovery of a compromised website.
Analyzes how U.S. federal IT security policies, while necessary, can stifle innovation and hinder adoption of modern, agile technologies.
Critique of counterproductive password policies, using Barclaycard as an example, and suggestions for more user-friendly, secure authentication.
Critique of Kenyan government proposals for internet cafe user logging and ISP deep packet inspection, framed as privacy overreach in the name of cybersecurity.