SHA1 and Richard Feynman
Discusses the importance of cryptographic safety factors, using SHA1's vulnerabilities and Feynman's Challenger report as analogies.
Discusses the importance of cryptographic safety factors, using SHA1's vulnerabilities and Feynman's Challenger report as analogies.
A proposal for PEP 543, which aims to create a unified TLS API for Python to address issues with the current standard library approach.
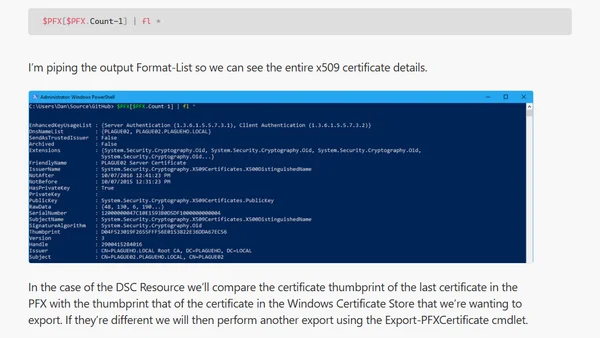
A technical guide on using PowerShell to read, analyze, and validate certificates within PFX files, including trust chain inspection.
A software engineer with extensive experience in open source, security, and multiple languages announces they are seeking a new role focused on impactful information security work.
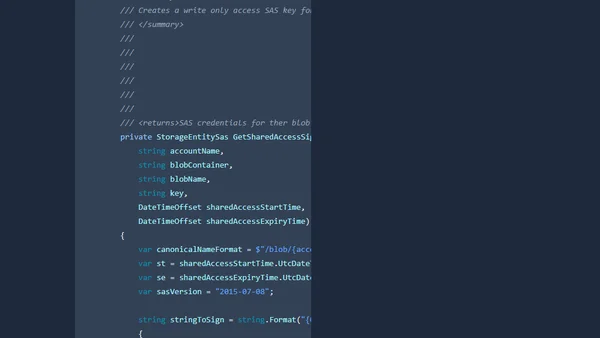
A technical guide on generating write-only Shared Access Signature (SAS) keys for Azure Blob Storage using .NET Core.
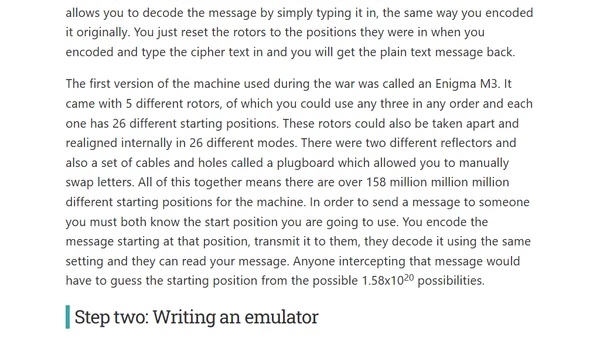
A developer explores parallel computing by writing a Go program to brute-force crack the WWII Enigma cipher, inspired by Alan Turing's work.

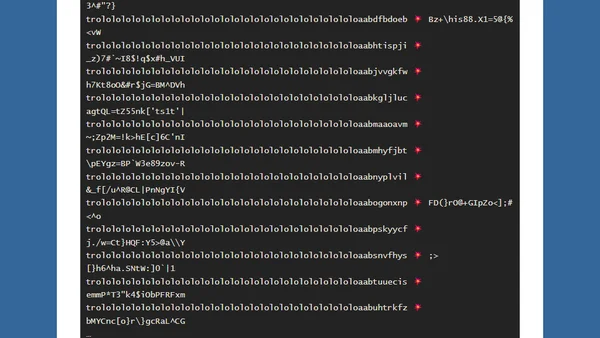
Analysis of a cryptographic vulnerability in the Beaker Python library's session encryption due to nonce reuse in AES-CTR mode.
Highlights five key projects advancing security: U2F, Let's Encrypt, Rust, X25519/Ed25519, and Chromebooks.
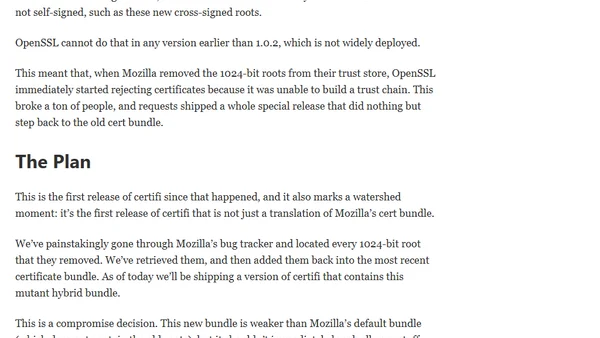
An update on the certifi project's new release, addressing 1024-bit root certificate removal and the plan for a hybrid bundle.
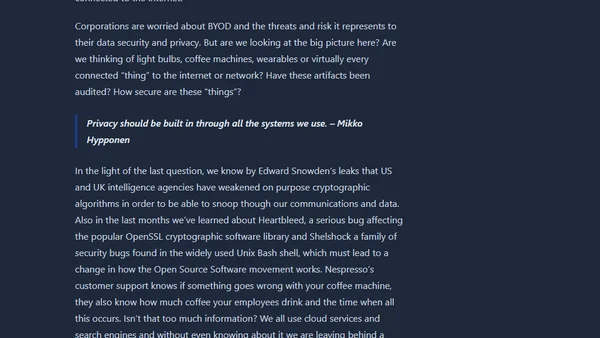
Analyzes the TV show Continuum to discuss real-world surveillance, IoT security risks, and the erosion of privacy in a connected world.
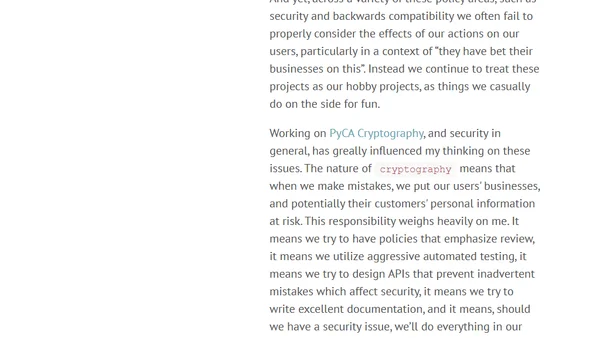
A reflection on the ethical responsibilities of open source maintainers, especially regarding security and user dependency, beyond the 'volunteer' excuse.
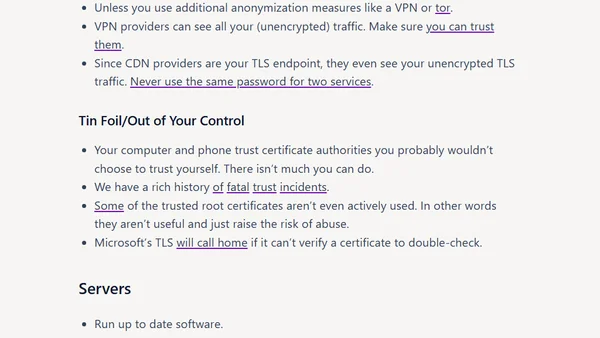
A technical talk on the challenges and proper implementation of TLS/SSL for secure communications, presented at multiple Python conferences.
Explains how and why two different strings produce the same PBKDF2-HMAC-SHA1 hash, detailing the cryptographic property behind the collision.
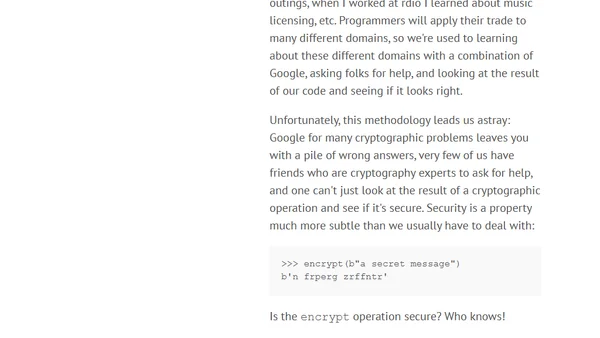
A programmer's journey into cryptography, sparked by a PyPy compatibility issue and the need for better, more secure cryptographic libraries in Python.
An article explaining cryptography and data security concepts, including a notable section on steganography.
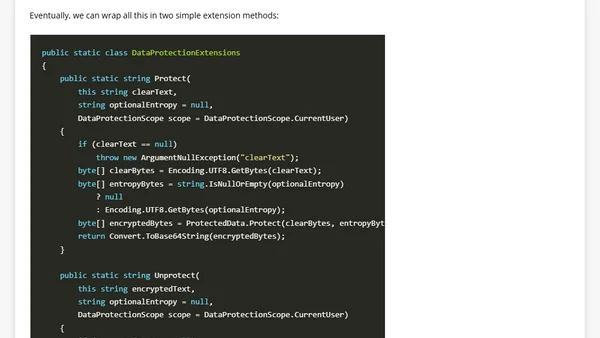
Explains how to securely store passwords in .NET using Windows Data Protection API (DPAPI) and the ProtectedData class.