Reviewing book – Learning Pentesting for Android Devices
A review of the book 'Learning Pentesting for Android Devices,' covering mobile security, reverse engineering, and network forensics for security professionals.
A review of the book 'Learning Pentesting for Android Devices,' covering mobile security, reverse engineering, and network forensics for security professionals.
Explores underutilized PostgreSQL data types like hstore, range types, timestamptz, and UUID, highlighting their benefits for specific use cases.
Explains the data and access impacts of deleting a user account from Visual Studio Online (now Azure DevOps).
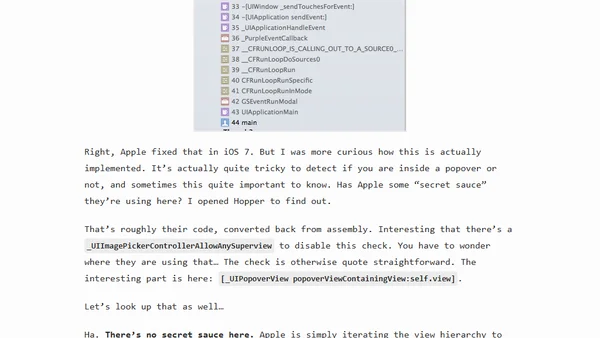
Introduces Aspects, an AOP library for iOS, and demonstrates using it to hack and debug Apple's private popover detection logic.
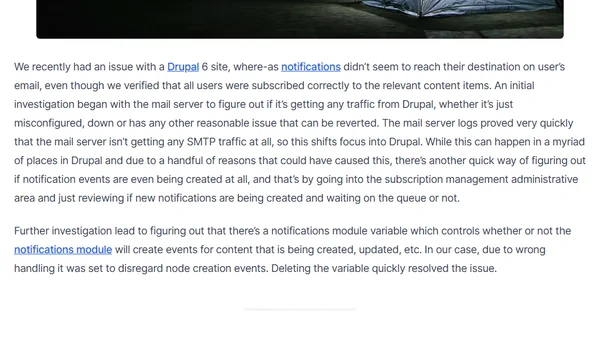
Troubleshooting guide for Drupal 6 email notification failures, focusing on a misconfigured module variable.
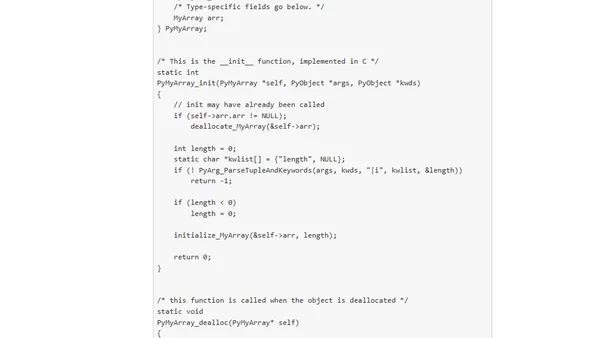
Explains the Python Buffer Protocol (PEP 3118), showing how objects like arrays and NumPy ndarrays share data efficiently without copying.
Introducing handroll, a simple static site generator for creating handcrafted websites with Markdown and templates.
A developer discusses why they included a 'respect' section in their open-source project's contributor guidelines, focusing on culture and security.
Fixing MongoDB Connector for Hadoop authentication errors by granting the clusterManager role to the user.
A developer's experience presenting on web accessibility and the Shadow DOM at JSConf Australia 2014, discussing the challenges of integrating accessibility into modern web development.
A practical guide to creating a minimal, functional R package from scratch to streamline code reuse and save development time.
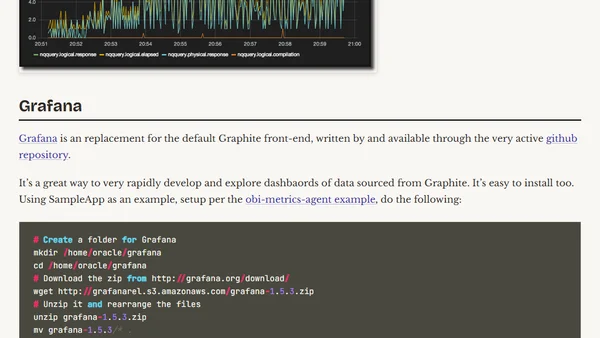
Extends OBIEE performance monitoring by integrating DMS metrics and nqquery.log data into Graphite and visualizing with Grafana.
A developer's post-mortem on an unfinished game, 'Mining Incorporated', created for the Ludum Dare 48-hour game jam.
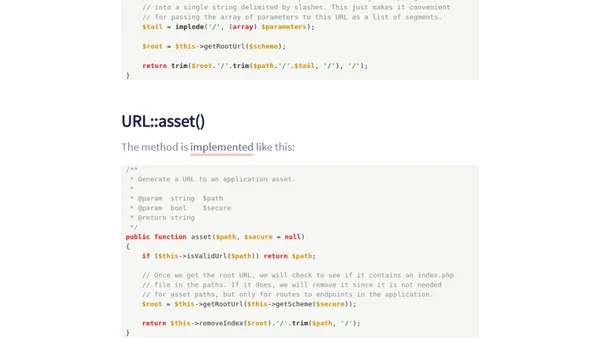
Explains the technical differences between Laravel's URL::to() and URL::asset() methods for generating URLs, including performance and use cases.

Explains new SQL Server 2014 permissions like IMPERSONATE ANY LOGIN and how they interact with CONTROL SERVER for security and privilege escalation.
A developer's early morning start on Ludum Dare 29, detailing initial coding progress and challenges with a game prototype.
A developer recounts leading a team at the NASA Space Apps hackathon, focusing on preparation and iterative development to build an asteroid mining game.
A developer's entry for the Ludum Dare 29 game jam, detailing their tech stack and preparation using C++ and SFML.
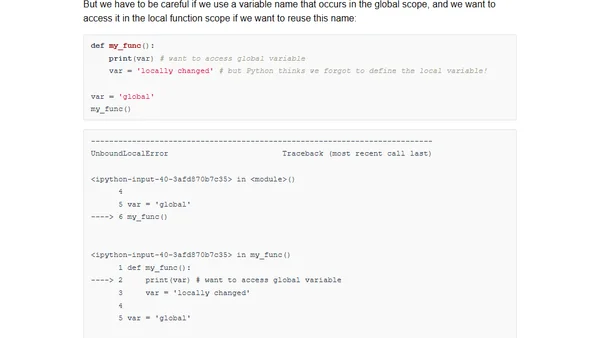
An in-depth exploration of Python's advanced features, quirks, and common pitfalls for experienced developers.
A blogger clarifies that Skype's unencrypted local database is not a security vulnerability, as it's protected by system-level access controls.