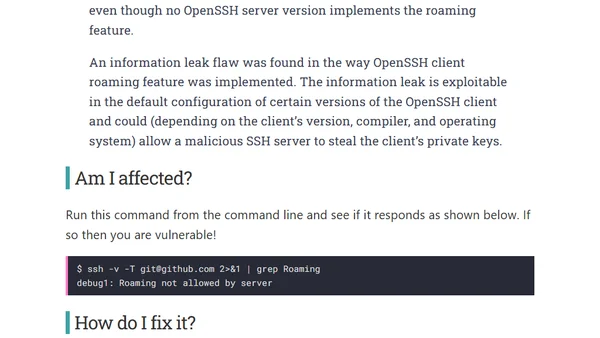
Fixing the SSH roaming vulnerability (CVE-2016-0777)
Details and fix for the OpenSSH client roaming vulnerability (CVE-2016-0777) that could allow a malicious server to steal private keys.
Details and fix for the OpenSSH client roaming vulnerability (CVE-2016-0777) that could allow a malicious server to steal private keys.
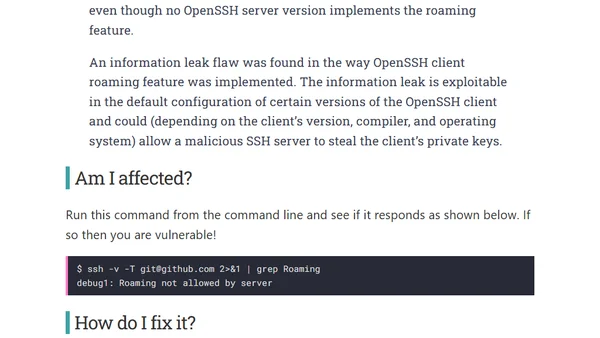
Learn how to securely manage VM passwords using Azure Key Vault secrets in ARM templates, eliminating plaintext password risks.
Highlights five key projects advancing security: U2F, Let's Encrypt, Rust, X25519/Ed25519, and Chromebooks.
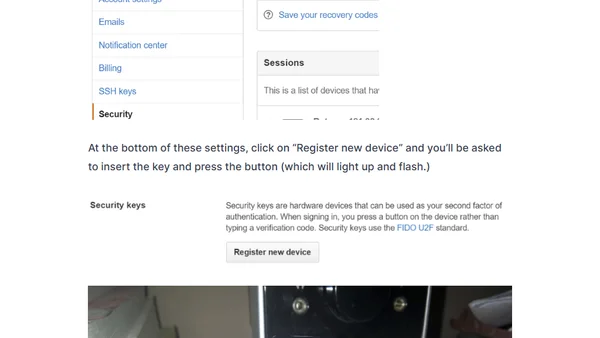
A developer's experience purchasing and setting up the special edition Octocat Yubico U2F security key for GitHub two-factor authentication.
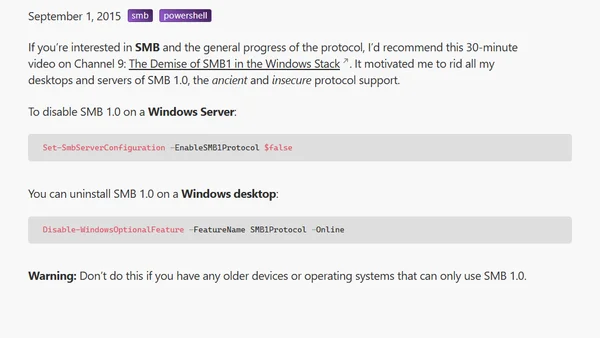
Discusses the deprecation of the insecure SMB1 protocol in Windows and provides PowerShell commands to disable or uninstall it.
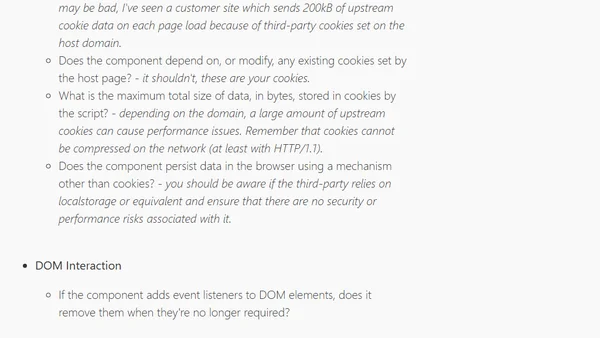
A guide on evaluating third-party scripts for web performance, security, and user experience, including a checklist of critical questions.
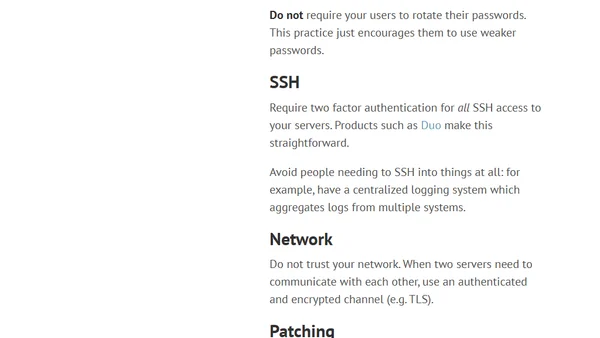
Practical advice for enhancing company security, covering password storage, SSH access, network encryption, patching, and developer education.
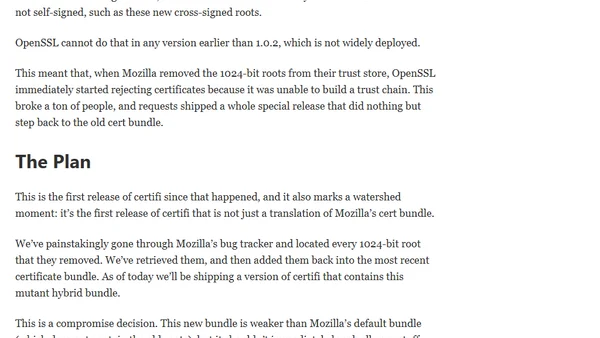
An update on the certifi project's new release, addressing 1024-bit root certificate removal and the plan for a hybrid bundle.
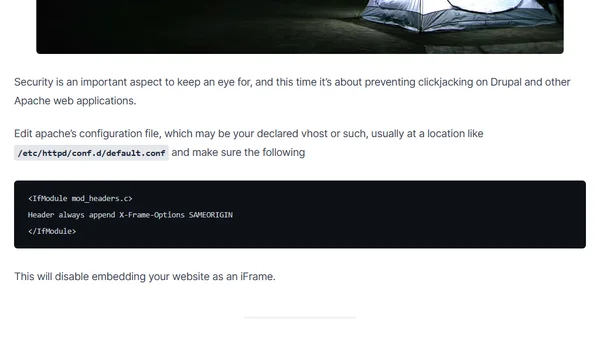
A guide to preventing clickjacking attacks on Drupal and Apache web applications by configuring the X-Frame-Options header.
A technical walkthrough on setting up and testing the Auditing feature in Azure SQL Database, including configuration and reporting.
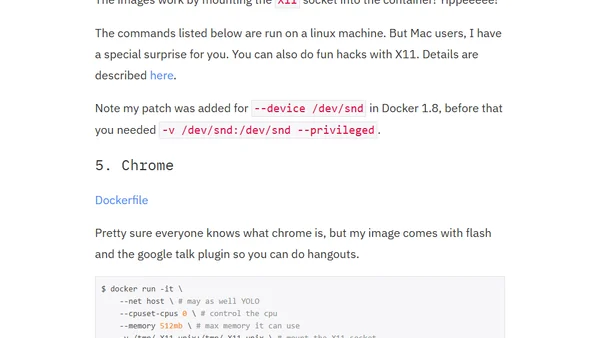
A guide on using Docker containers to run desktop applications like IRC clients and email, offering isolation and resource control.
A guide to securing the ASP.NET MVC Web.config file, covering custom errors, cookie security, and removing revealing HTTP headers.

A technical guide to achieving an A+ SSL/TLS rating on Qualys SSL Labs by configuring Nginx with specific protocols, ciphers, and security features.
A comprehensive guide to implementing favicons and related icons for modern websites, covering various devices and platforms with ASP.NET MVC examples.
An overview of ASP.NET Core Boilerplate, a professional template for building secure, fast, and SEO-friendly web applications with improvements over the default MVC template.
Essential security practices for freelance developers, covering device locking, password management, and multi-factor authentication.
Explains AWS authentication options like root accounts and IAM users, focusing on security best practices and access control.
Argues that HTTPS requires certificate verification for security, discussing Python's debate on backporting this fix to version 2.7.
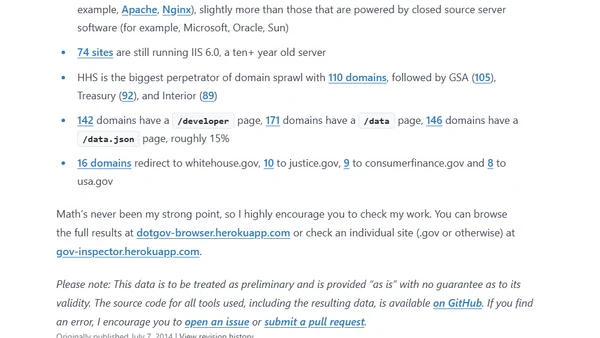
A follow-up analysis of U.S. federal .gov domains, tracking changes in technology, security, and accessibility over three years.
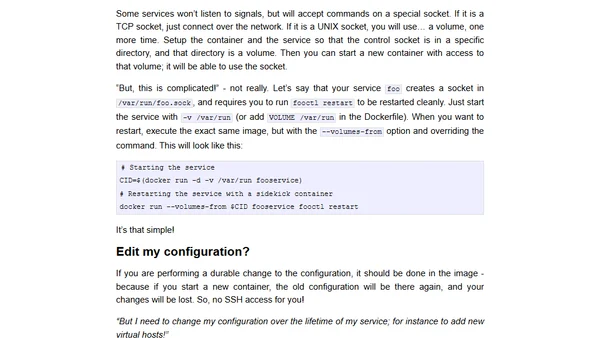
Explains why running SSH servers in Docker containers is bad practice and recommends better alternatives for debugging and management.