Fighting npm typosquatting attacks and naming rules for npm modules
Explains npm's evolving naming rules to combat typosquatting attacks, detailing case sensitivity and character restrictions for package names.
Explains npm's evolving naming rules to combat typosquatting attacks, detailing case sensitivity and character restrictions for package names.
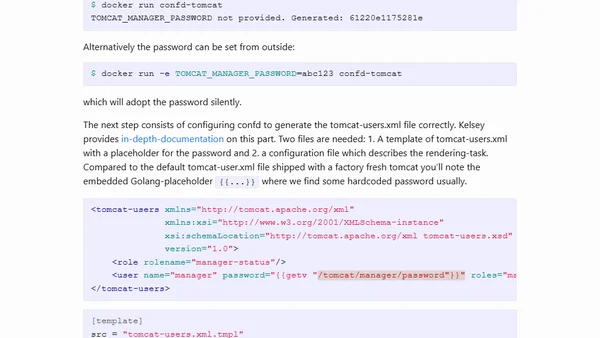
A guide on using confd to dynamically generate Tomcat configuration files and eliminate hardcoded passwords in Docker containers.
A critical analysis of Signal's security model, focusing on its reliance on Google Play Services and resistance to F-Droid distribution.
Explains Bitcoin's security as a spectrum, not binary, using analogies and discussing confirmations, threat models, and double-spend protection.
Explains security risks in the npm ecosystem, including malicious modules, typosquatting, and compromised contributors, with mitigation advice.
Explains a key security change in ASP.NET Core 2.1 where authorization filters are combined, altering authentication and role-checking behavior.
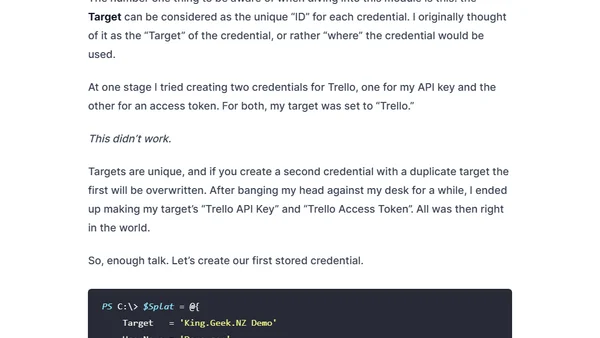
A guide to securely storing and accessing script credentials using the Windows Credential Manager and a PowerShell module.
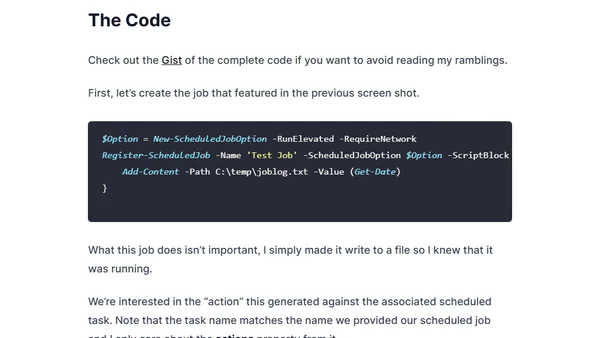
Explains how to specify the full path to PowerShell.exe in Windows Scheduled Jobs for improved security, preventing path interception attacks.
A compilation of technical talks on open source firmware, container security, Intel SGX, and cloud-native infrastructure from 2017-2019.
An introduction to the Node.js Security Working Group, its role in securing Node.js core and modules, and how to get involved.
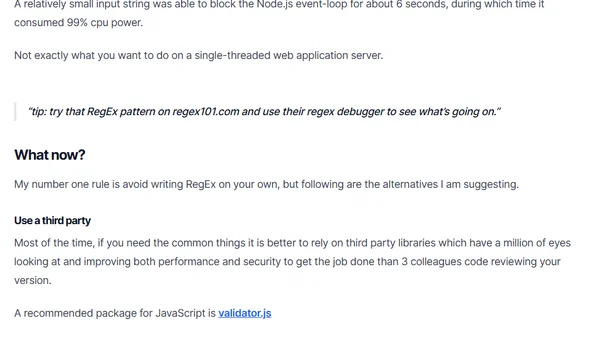
Explains how flawed Regular Expressions can cause ReDoS attacks, crippling Node.js services with catastrophic backtracking and high CPU usage.
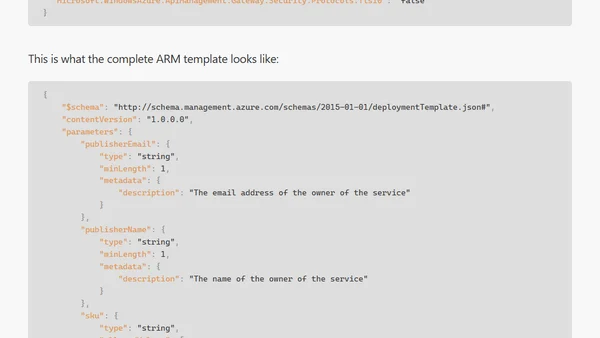
Guide to disabling outdated TLS protocols and ciphers in Azure API Management using ARM templates for improved security.
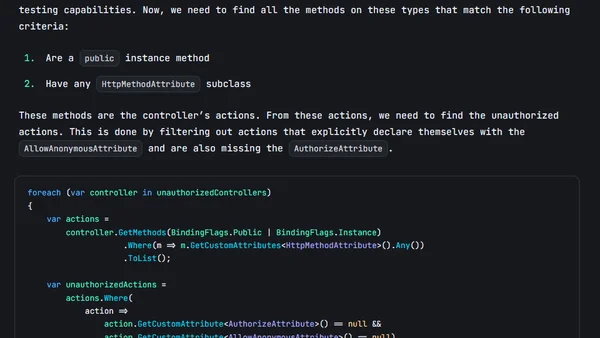
A guide to writing unit tests in ASP.NET Core to automatically verify that security attributes like AuthorizeAttribute are applied to controllers and actions.
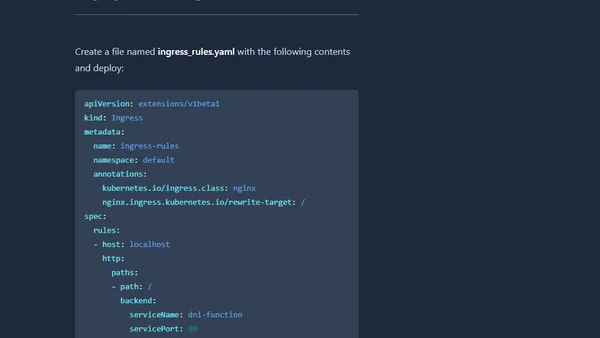
A technical guide on securing Kubernetes services using NGINX Ingress Controller, covering TLS setup, whitelisting, and rate limiting.
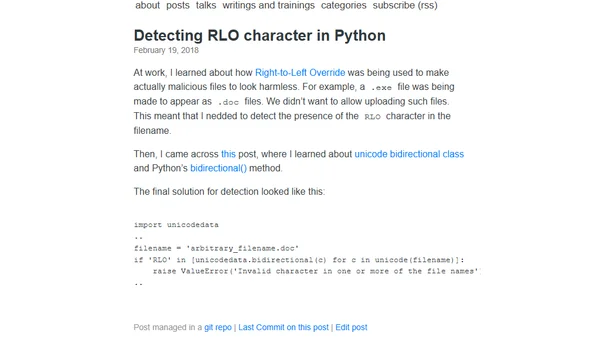
How to detect Right-to-Left Override (RLO) characters in filenames using Python's unicodedata module to prevent malicious file spoofing.

A technical guide to building and enhancing a secure, accessible login form with HTML validation, security best practices, and UX improvements.
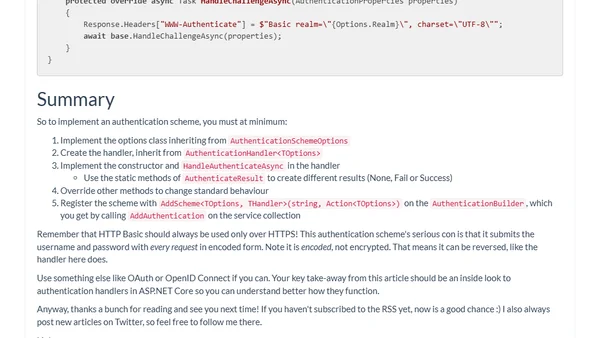
A tutorial on implementing a custom HTTP Basic authentication scheme within the ASP.NET Core 2.0 authentication framework.

A survey asking readers about their patching status for the Meltdown and Spectre CPU security vulnerabilities, with results shared.

Analysis of the Meltdown/Spectre processor flaws and their critical impact on SQL Server deployments, security, and performance.
Analyzes the recent panic over npm security, arguing it's based on social engineering in PRs, not a flaw in npm itself.