Fully Qualified Path to PowerShell.exe in Scheduled Jobs?
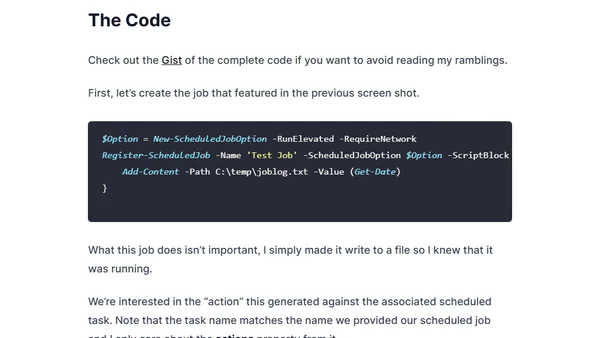
Read OriginalThis technical article addresses a security concern in Windows PowerShell scheduled jobs, where using just 'powershell.exe' could allow a malicious executable to be intercepted. It provides a step-by-step guide and code examples to modify the scheduled job's action to use the fully qualified path (C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe) via PowerShell commands, avoiding the GUI.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser