Choosing a VPN service is a serious decision
A critical analysis of VPN services, highlighting privacy risks and the importance of researching providers before use.
A critical analysis of VPN services, highlighting privacy risks and the importance of researching providers before use.
Guide to enabling TLS 1.2 support in legacy .NET applications without recompilation, using configuration file updates.
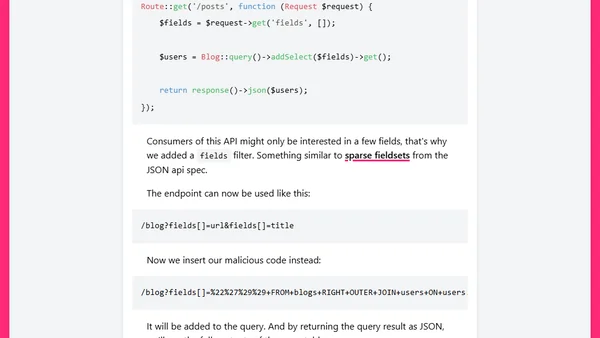
Explains SQL injection risks in Laravel's query builder, focusing on unsafe functions like addSelect and JSON shorthand, with a fixed vulnerability example.
Analysis of a malicious backdoor discovered in the popular bootstrap-sass Ruby gem, its impact, and essential security best practices for developers.
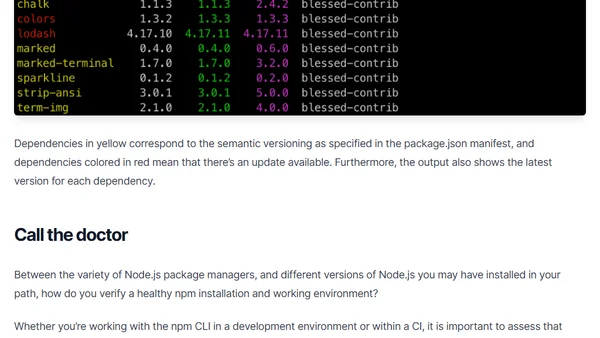
Learn how to use npm outdated and npm doctor commands to assess your project's dependency health and environment setup.
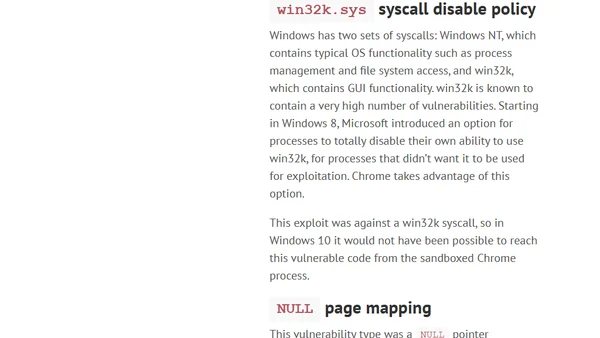
Analysis of a Chrome/Windows exploit chain, explaining why Windows 10 mitigations make it harder to exploit than on Windows 7.
A developer's updated reflections on Intel SGX technology, considering its original DRM purpose and new use cases for secure cloud execution.
Part 6 of a series on AWS serverless mistakes, focusing on security best practices like IAM roles, secret management, and OWASP risks.

Part 2 of a series on championing third-party observability tools to your security team, focusing on building empathy and alignment.
A guide on championing third-party observability services to security teams, featuring expert advice in a three-part series.
Analysis of fuzzing ImageMagick and GraphicsMagick with OSS-Fuzz, revealing hundreds of security bugs despite prior audits.
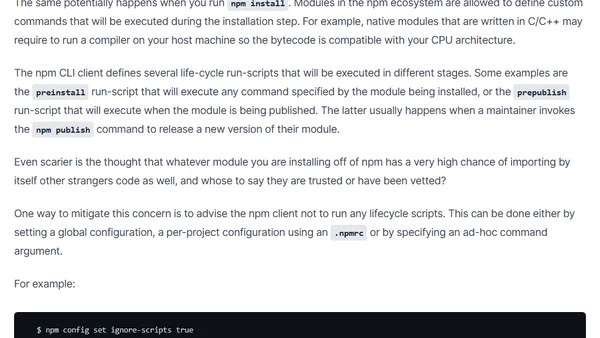
Analyzes security risks in npm package installation, highlighting the dangers of arbitrary code execution and advocating for cautious dependency management.
Highlights from the Node.js Security WG's January 2019 meeting, covering bounty programs and vulnerability database improvements.
A guide for ASP.NET MVC Core developers on identifying and adding CSRF protection to an inherited codebase lacking security measures.
Analyzes the security concerns and evolving best practices for the OAuth2 implicit flow, especially for browser-based applications.
The article argues for optimizing code for auditability to make security vulnerabilities easier to spot, using cryptography as a key example.
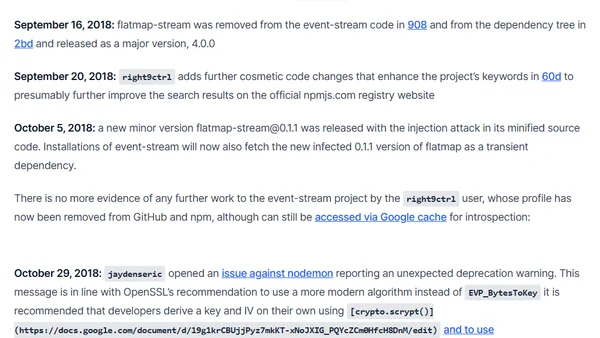
A detailed analysis of the malicious event-stream npm package backdoor, its timeline, and the social engineering attack that led to its inclusion.
Explains the purpose of React's $$typeof property, a security feature using Symbols to prevent XSS attacks in React elements.
A guide explaining four types of files you should avoid committing to a Git repository, including project-irrelevant files, generated code, libraries, and credentials.
A guide on securely storing sensitive configuration data in .NET Core applications, covering sources like User Secrets and Environment Variables.