On Safety Critical Software
Explores the challenge of building safety-critical software for high-risk users like activists, contrasting it with mainstream security needs.
Explores the challenge of building safety-critical software for high-risk users like activists, contrasting it with mainstream security needs.
A technical comparison of built-in security features and secure coding practices in React and Angular frameworks.
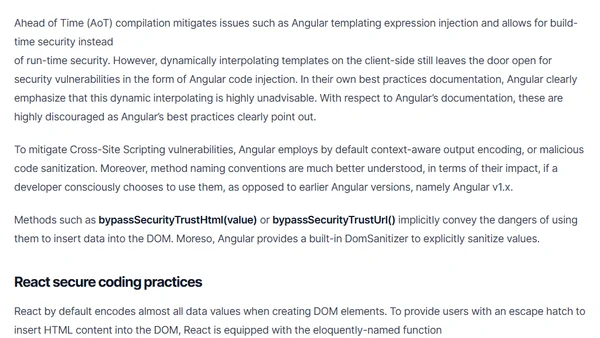
A guide to using SSH efficiently from the terminal, covering key generation, SSH agent setup, and best practices for secure remote access.
A speaker discusses using Azure Managed Identities to securely access services without managing keys, including a demo app for file sharing.
Azure AD now blocks cross-tenant token attacks by preventing apps from getting tokens for tenants where they have no service principal.
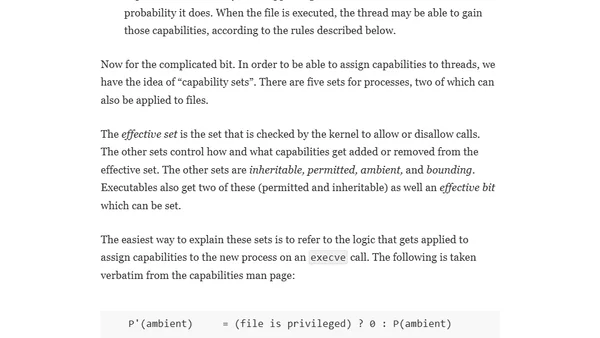
Explains the history and mechanics of Linux capabilities, a security model for granular process privileges, and their interaction with containers.
Essential npm security best practices to protect against malicious packages, including ignoring run-scripts and vetting third-party modules.
Explores SQL Server 2019's new 'Feature Restrictions' security feature, designed to help prevent SQL injection attacks.
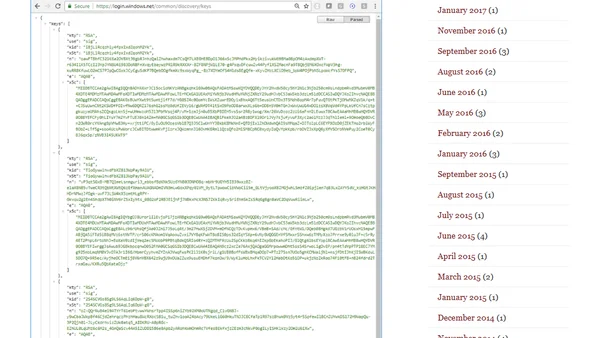
Explains the process and importance of rotating signing keys in IdentityServer for security, detailing the use of AddSigningCredential and AddValidationKey.
Explains security risks and best practices for managing user permissions in Django's admin interface to prevent data leaks.
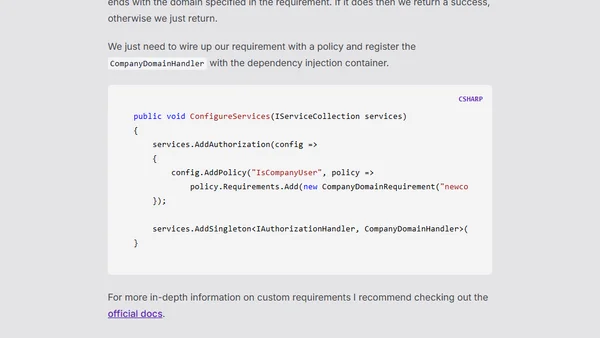
A guide to implementing policy-based authorization in Blazor applications, covering setup, advantages over role-based auth, and custom requirements.
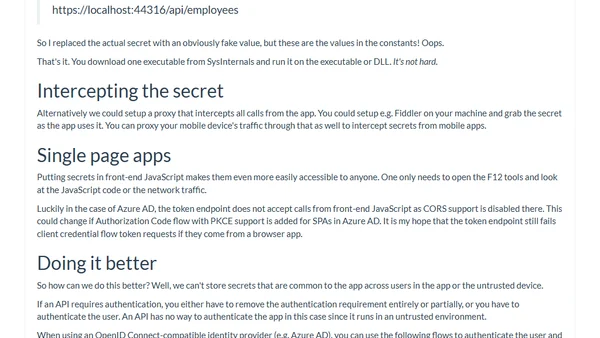
Explains why embedding secrets like API keys in native apps is a critical security flaw, with a practical demonstration.
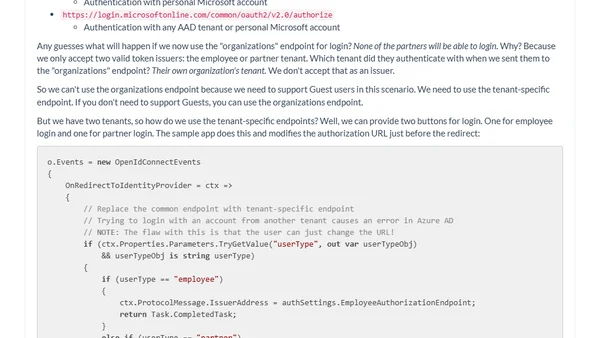
Explains best practices for building secure multi-tenant Azure AD applications that restrict login to a specific set of known tenants.
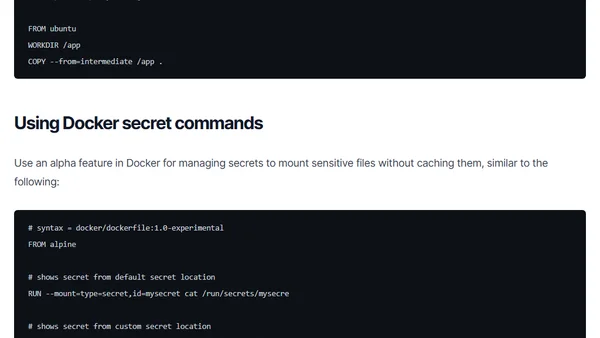
Learn how to prevent secrets like SSH keys and API tokens from being leaked into your final Docker images using multi-stage builds and secrets management.
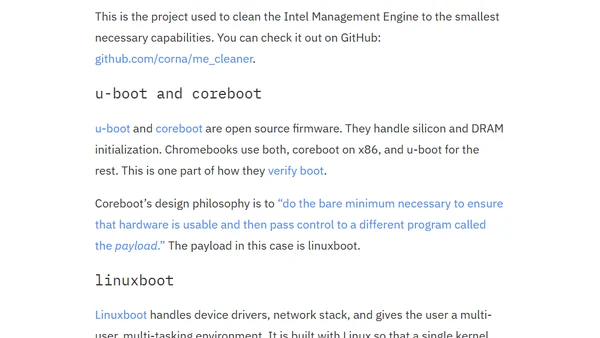
Explains the security risks of proprietary firmware in deep system privilege levels (Rings -2 & -3) and advocates for open source alternatives.
A delegate's analysis of Rubrik's Cloud Field Day 5 presentation, focusing on their Polaris platform and its potential beyond ransomware detection.

Explains the OAuth Resource Owner Password Credentials (ROPC) grant flow in Azure AD, detailing its purpose and why it should be avoided in modern applications.
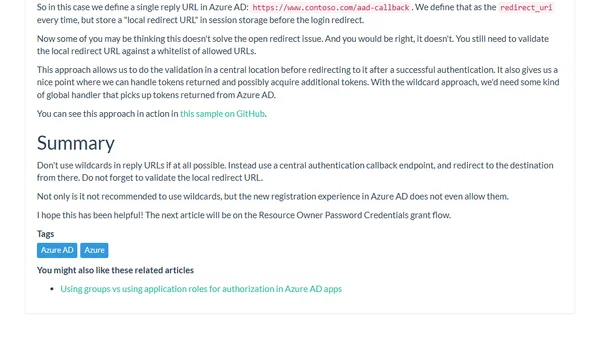
Explains security risks of wildcard reply URLs in MSAL.js and demonstrates a safer alternative using session storage for post-login redirects.
An analysis of Sysdig's cloud-native monitoring solution, which uses eBPF for container security and performance insights.
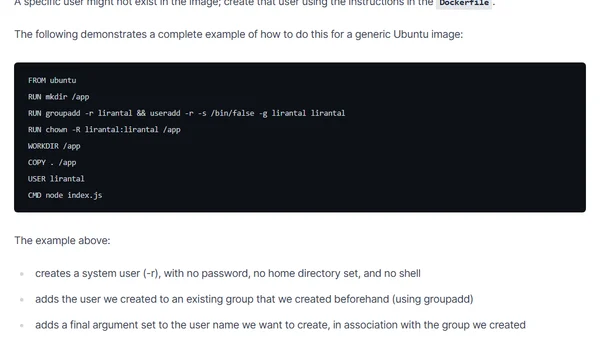
A guide on implementing Docker security best practices for Node.js, focusing on using non-root users to minimize attack surfaces.