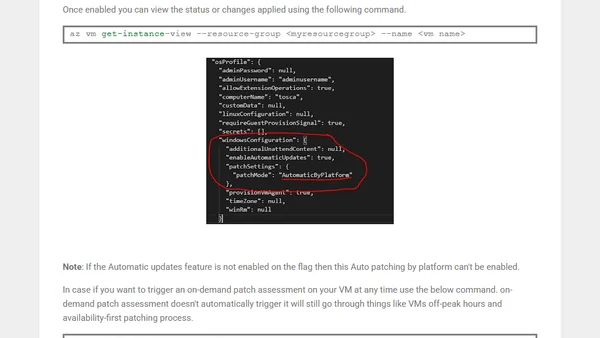
How to enable Automatic Guest OS Patching for Windows Azure VMs?
Guide to enabling Automatic Guest OS Patching for Windows Azure VMs, a public preview feature for automated security updates.
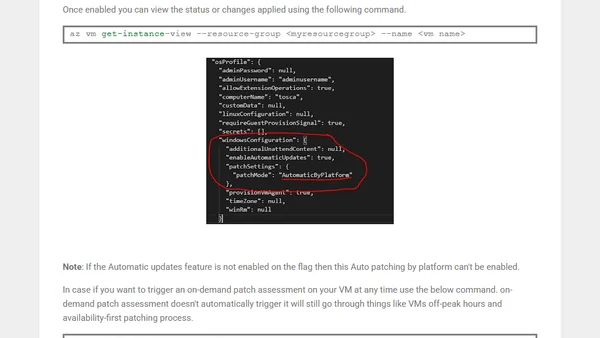
Guide to enabling Automatic Guest OS Patching for Windows Azure VMs, a public preview feature for automated security updates.
A threat modeling case study using bicycle theft to illustrate security principles applicable to IT systems.
A guide on using the Terminal command `spctl` to verify if a macOS application has been notarized by Apple.
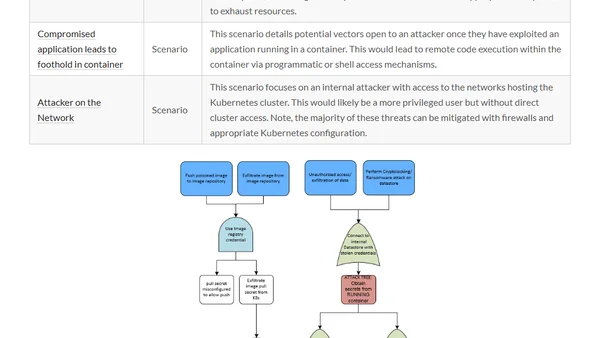
A summary of three major Kubernetes threat modeling initiatives to help security professionals secure their production clusters.
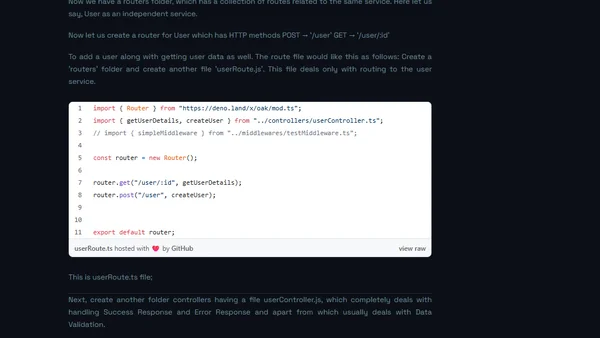
A technical analysis comparing Deno and Node.js, focusing on Deno's design improvements like security, URL imports, and eliminating node_modules.
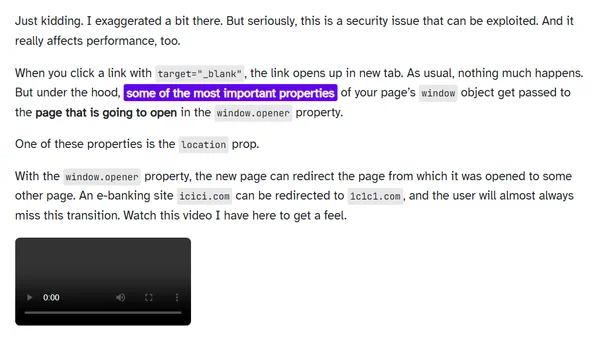
Explains the security and performance risks of using target=_blank links without rel="noopener" and provides the simple fix.
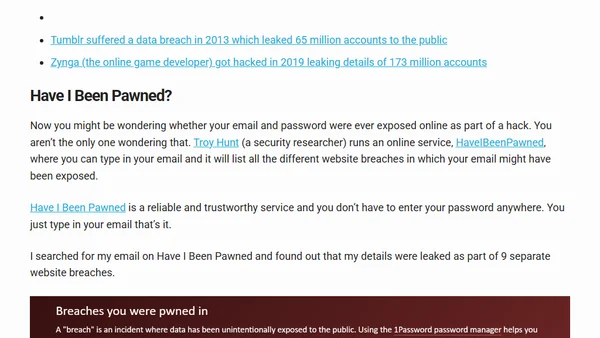
A detailed analysis of a blackmail email scam demanding a $2000 Bitcoin payment to prevent the release of compromising material.
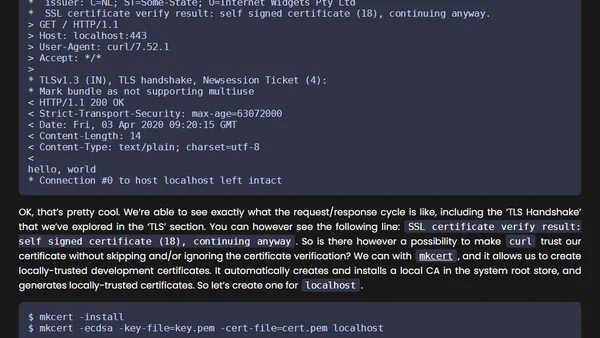
A guide to implementing security best practices for Go HTTP webservers, covering timeouts, TLS, and other hardening measures.
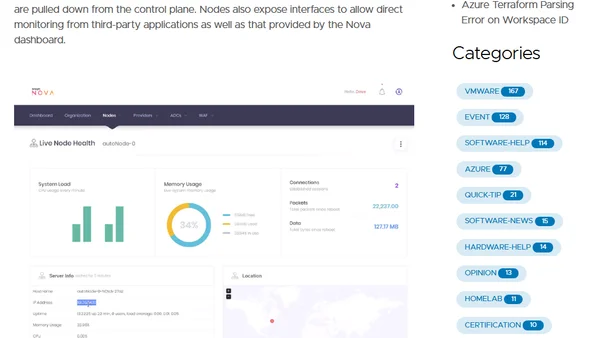
A review of Snapt's Nova platform for multi-cloud load balancing, web acceleration, and security, presented at a virtual IT event.
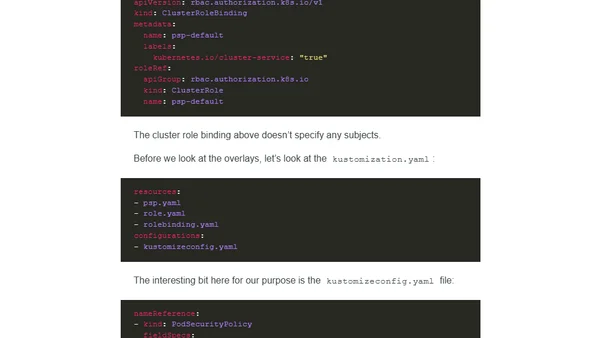
A technical guide explaining Kubernetes Pod Security Policies (PSP), their enforcement, and management using tools like kustomize.
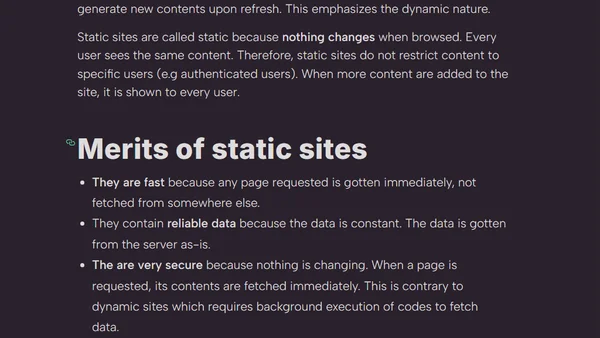
Explains static site generators (SSGs), their benefits for speed and security, and contrasts them with dynamic websites.
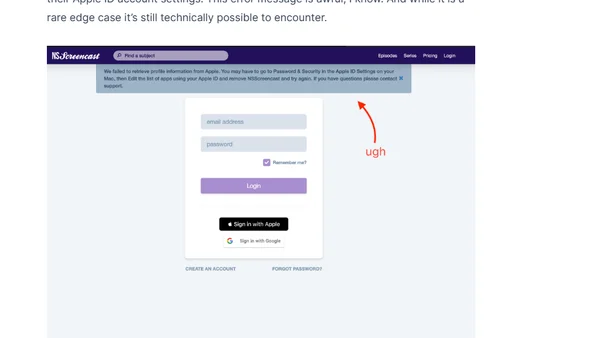
A developer's guide to implementing Sign-in with Apple, focusing on challenges with one-time profile data and security considerations.
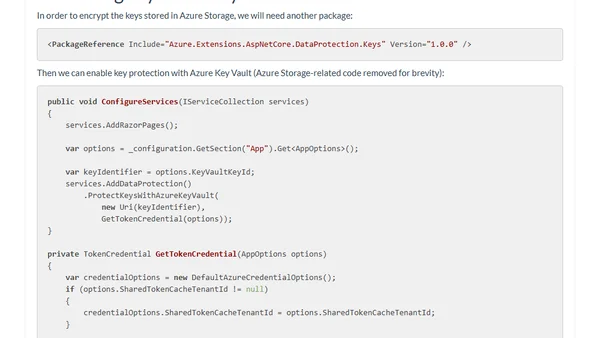
Guide to securely storing ASP.NET Core Data Protection keys using Azure Key Vault for encryption and Azure Blob Storage for persistence.
A software expert's open letter opposing the EARN IT Act, arguing it threatens essential end-to-end encryption and digital freedoms.
Explores common issues and solutions when implementing Keychain Sharing for iOS app extensions, covering group names, simulator limitations, and entitlements.
A review of 2019 security predictions, covering progress on Rust adoption, WebAuthn security keys, and TLS 1.3 deployment.
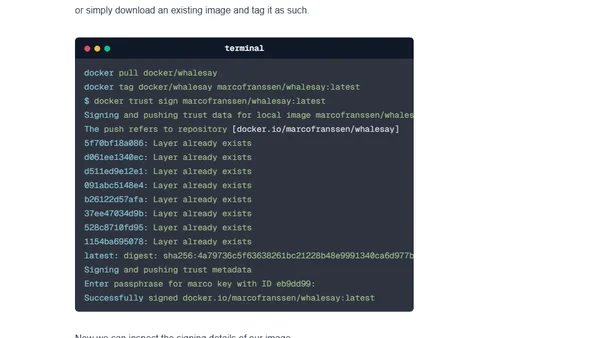
A guide to using Docker Content Trust (DCT) to digitally sign Docker images, ensuring integrity and publisher authenticity.
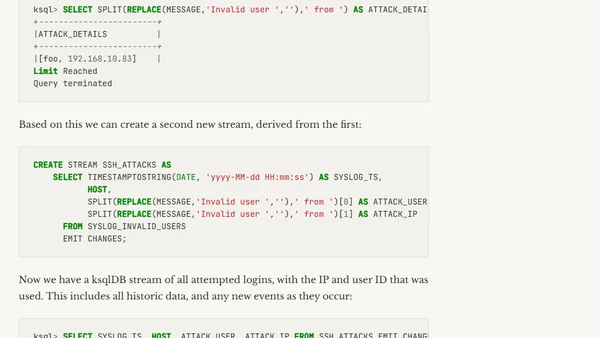
A technical guide on using ksqlDB and Kafka Connect to ingest and analyze Syslog data for detecting SSH attacks.
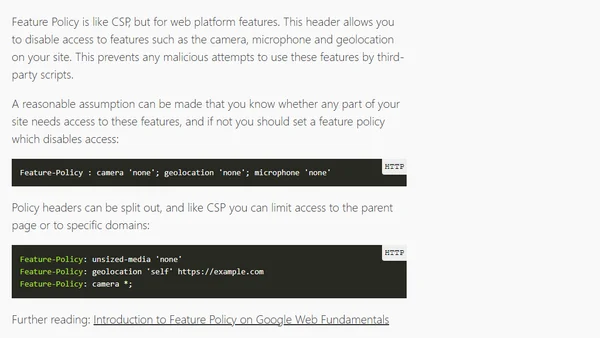
A guide to configuring essential HTTP response headers like Content-Security-Policy and Cache-Control for improved security and performance on static sites hosted on Netlify.
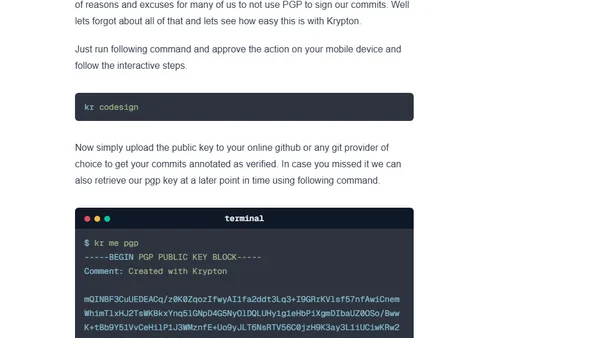
A tutorial on setting up two-factor authentication for SSH and PGP keys using the Krypton tool, storing keys on a mobile device.