Windows Server Event Log and Event Log Policies
A guide to understanding, configuring, and managing Windows Server Event Logs for effective monitoring, troubleshooting, and security.
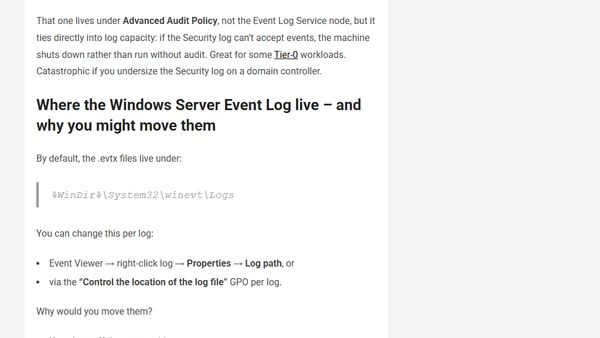
A guide to understanding, configuring, and managing Windows Server Event Logs for effective monitoring, troubleshooting, and security.

Explores advanced techniques attackers use to bypass SQL Server data access auditing and provides mitigation strategies to close security gaps.

A guide to implementing essential security auditing for databases, using Microsoft SQL Server as a practical example to demonstrate configuration and importance.

SQL Server auditing fails to capture permission change attempts, creating a security gap. Article details the issue and a temporary workaround.
Explains how to analyze and audit Azure AD Conditional Access policies using Microsoft Sentinel and KQL queries for security insights.

Explains the security concept of Audit Trails in SQL Server, covering their purpose, implementation, and importance for incident response.
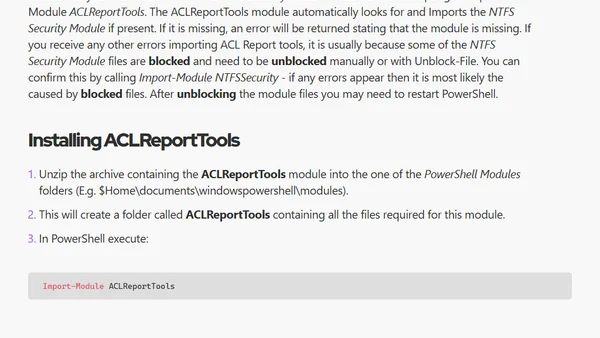
Introduces a PowerShell module for tracking and reporting changes to file, folder, and share permissions (ACLs) over time for security auditing.