Transferring a Google Fi eSIM on iOS
A guide on transferring a Google Fi eSIM to a new iPhone, including steps and security considerations for travelers.
A guide on transferring a Google Fi eSIM to a new iPhone, including steps and security considerations for travelers.
A comprehensive guide to all OAuth 2.0 grant types, explaining their flows and use cases for secure application authorization.
A guide to fixing AsyncStorage warnings when using Firebase JS SDK with React Native by properly configuring the auth persistence layer.
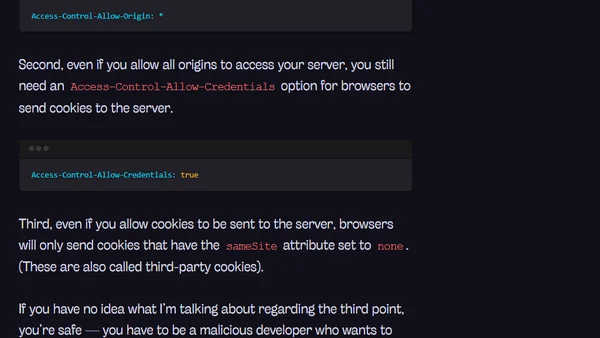
A clear, step-by-step guide explaining what CSRF attacks are, how they work, and the prerequisites needed for them to succeed.
A developer shares practical tips and warnings for using YubiKeys for 2FA, SSH authentication, and sudo prompts to enhance security.
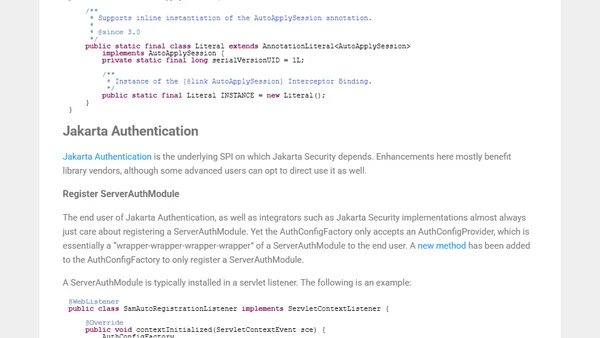
Jakarta Security 3's major update introduces OpenID Connect authentication, alongside its core API and underlying SPIs for Jakarta EE.
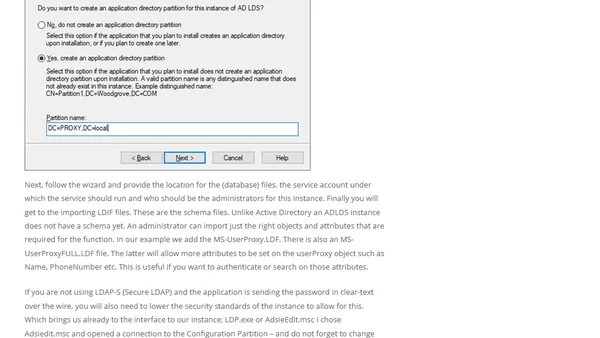
Explains using an LDAP Proxy with AD LDS to authenticate legacy applications during Active Directory migrations without rewriting them.
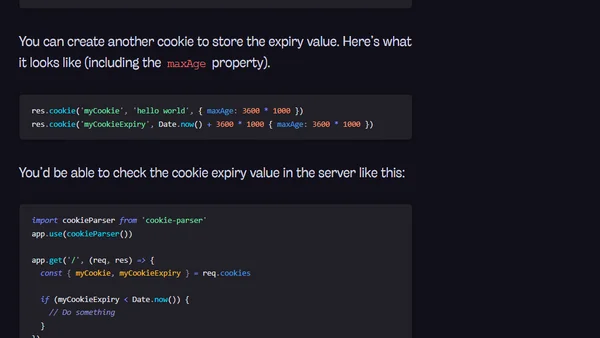
Explains two methods to access a cookie's expiration value on the server, which browsers normally don't send.
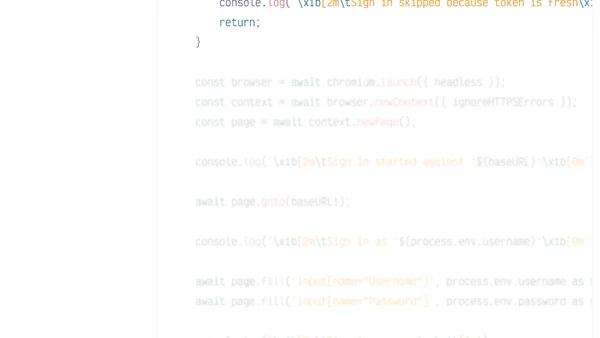
A guide to implementing efficient authentication state reuse in Playwright end-to-end tests to avoid repeated logins and speed up test suites.
A technical guide explaining how to authenticate and connect to an Azure AD B2C tenant using Azure CLI and PowerShell Az module.
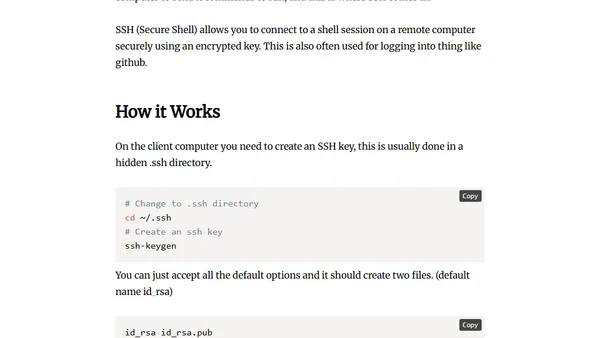
Explains SSH (Secure Shell), its purpose for secure remote computer connections, and how to generate and use SSH keys.
A critical analysis of Plaid's security model, arguing its credential collection widget undermines decades of online banking security best practices.
Exploring Azure AD B2C's 'Seamless Migration' feature for moving user identities to the cloud with minimal friction.
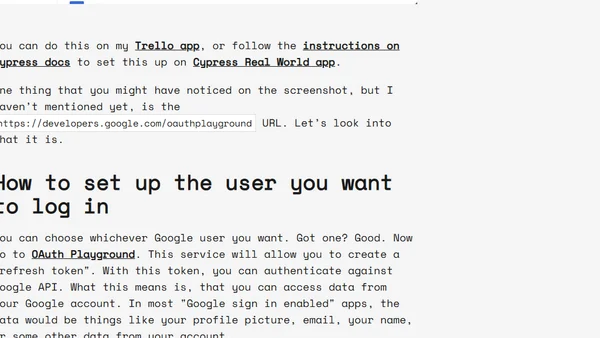
A technical guide on how to programmatically handle Google Sign-In (OAuth 2.0) in Cypress tests, bypassing multi-domain limitations.

A guide to calling the Kubernetes API directly using HTTP clients like curl, covering authentication, server discovery, and CRUD operations.

A tutorial on implementing a one-to-many database relationship with user authentication using the Masonite framework in Python.
A developer-focused guide on password management best practices, including secure storage, length recommendations, and multi-factor authentication.
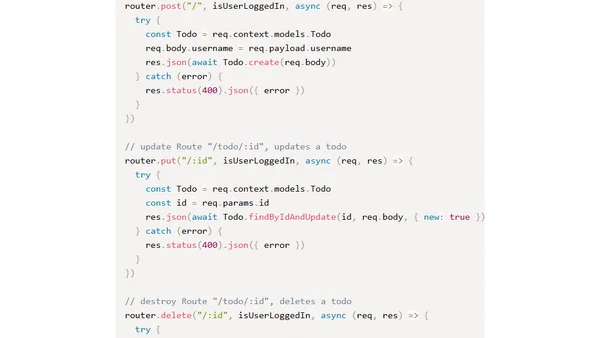
A tutorial on implementing JWT authentication in an Express.js API, with examples using both MongoDB and PostgreSQL databases.
A technical guide explaining how to implement authentication and authorization in any backend language or framework, covering user models, signup/login routes, and session vs JWT auth.
Explains disk encryption basics for non-technical users, covering why it's needed, how it works, and different implementation types.