Analyzing Workload Identity Activity Through Token-Based Hunting
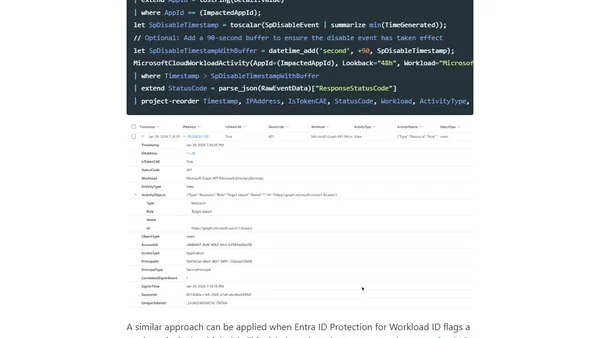
Read OriginalThis article details the creation and use of a custom KQL function, 'MicrosoftCloudWorkloadActivity', for security monitoring. It explains how to hunt for anomalous token usage by non-human identities (applications, service principals) in Microsoft Entra, covering the query's logic, data sources, and its importance due to the high risk and limited security controls for workload identities.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser