How to intercept the “run as administrator” event
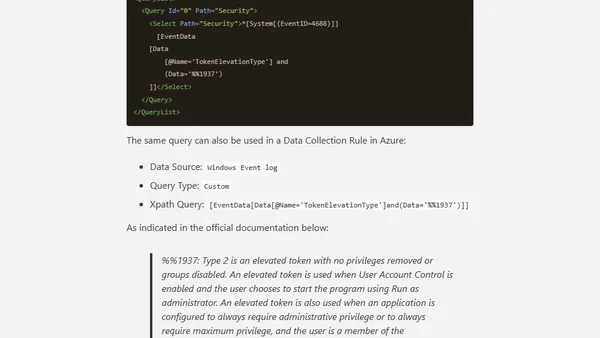
Read OriginalThis article provides a detailed tutorial on how to detect when a user executes a program with 'Run as Administrator' on Windows. It explains monitoring Event ID 4688, checking the Token Elevation Type field for value %%1937, enabling the necessary audit policy, and using specific XPath queries for filtering in Windows Event Viewer and Azure Data Collection Rules.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser