Restore accidentally deleted/replaced binary of a running process
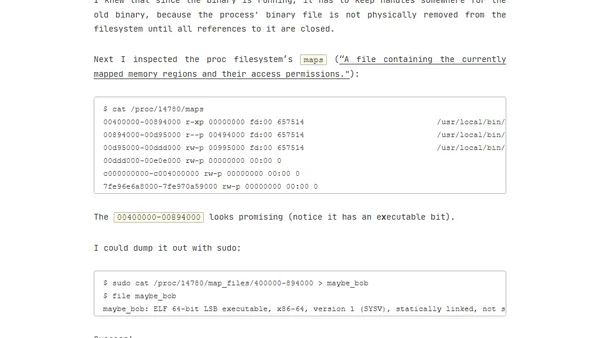
Read OriginalThe article details a technical challenge where the author accidentally overwrote a buggy build system binary, creating a chicken-and-egg problem. It explains the solution: identifying the running process's PID, examining /proc/[pid]/maps to find the memory-mapped executable regions, and dumping the binary from /proc/[pid]/map_files/ to restore the working version.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser