Surprising Consequences of macOS’s Environment Variable Sanitization
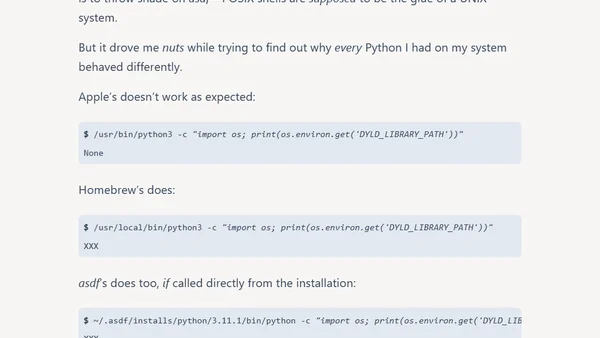
Read OriginalThis technical article details macOS's System Integrity Protection (SIP) and its sanitization of DYLD_* environment variables like DYLD_LIBRARY_PATH, which can break database drivers and other tools. It explores the problem's scope across shells, build tools like Make, and command runners, providing practical workarounds for developers needing to bypass this security feature.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser