Exploring kubernetes privileged pods
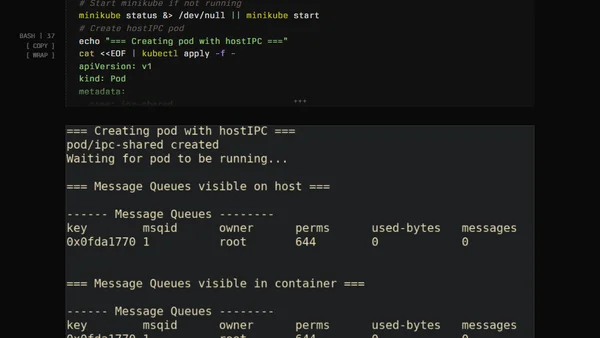
Read OriginalThis technical article investigates the Linux namespace isolation of privileged Kubernetes pods. It clarifies that setting `privileged: true` grants broad Linux capabilities but does not automatically share host namespaces like network, PID, or IPC. The author details findings from testing, showing that only the user namespace is shared by default, and explains how specific pod specs (hostNetwork, hostPID, hostIPC) control actual namespace sharing.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser