Understanding MCP Authorization, Step by Step, Part Three
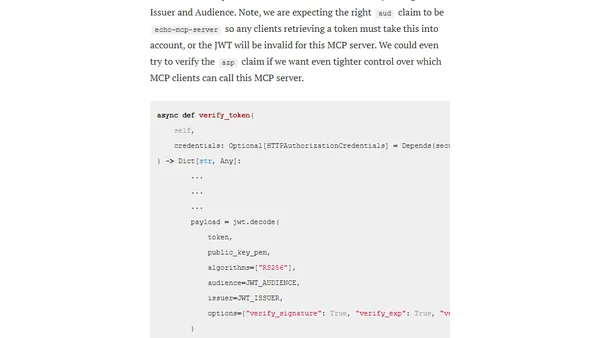
Read OriginalThis article is the third and final part of a technical series on MCP Authorization following the June 2025 spec. It details steps to replace a local identity provider with a production-ready one (Keycloak), covering setup, configuration, and token verification. It includes code examples and GitHub references for implementing OAuth 2.1 authorization in an MCP server.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser